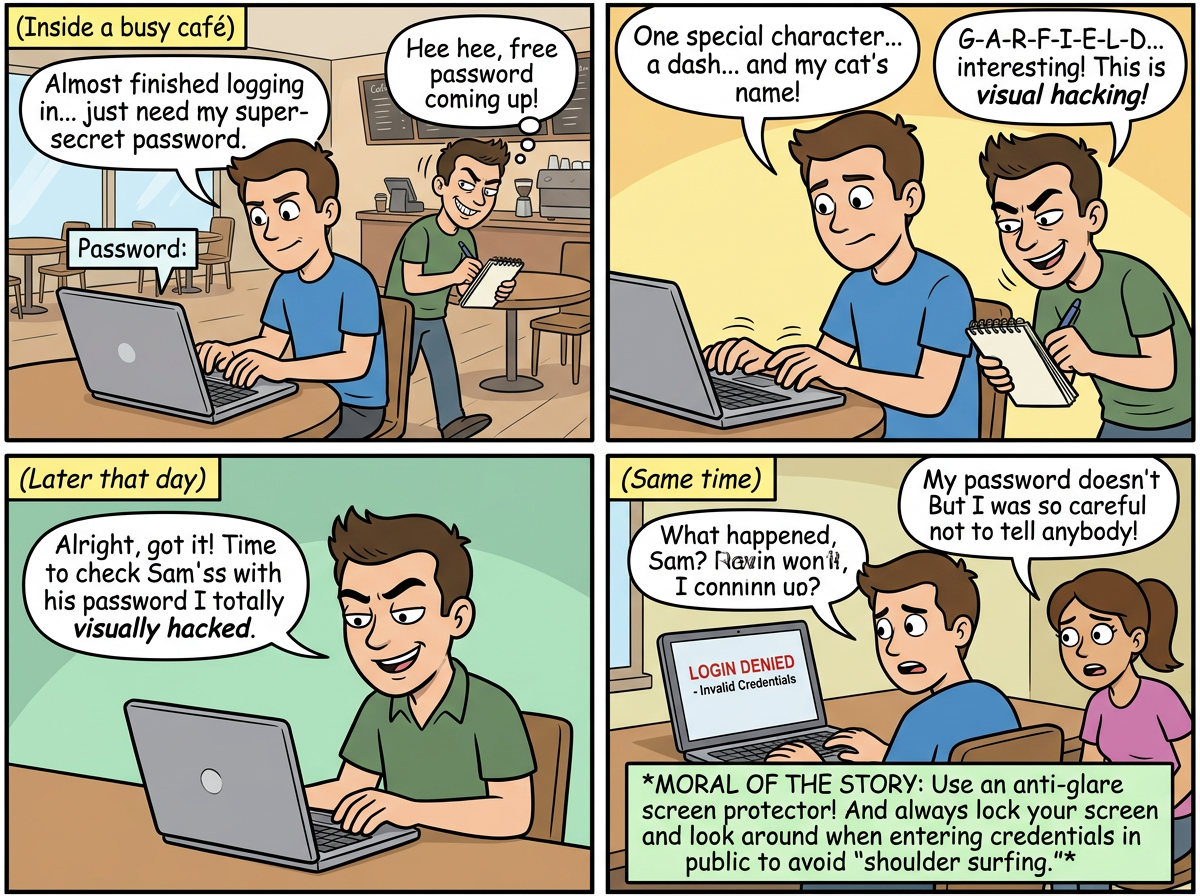
CyberToons: shoulder surfing and visual hacking
Learn about shoulder surfing and visual hacking through our educational cybersecurity comic....
68 comics about cybersecurity
Learn about shoulder surfing and visual hacking through our educational cybersecurity comic....
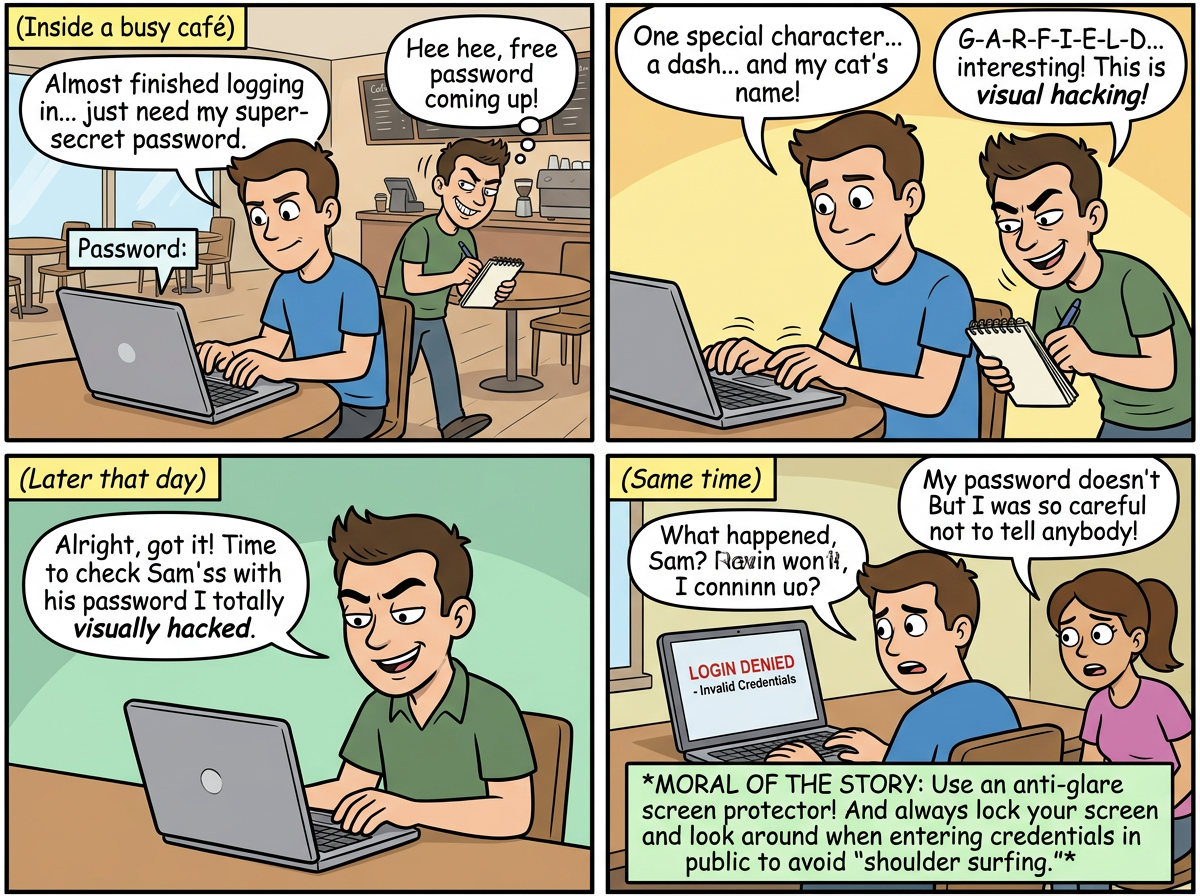
Learn about romance scams and catfishing through our educational cybersecurity comic....
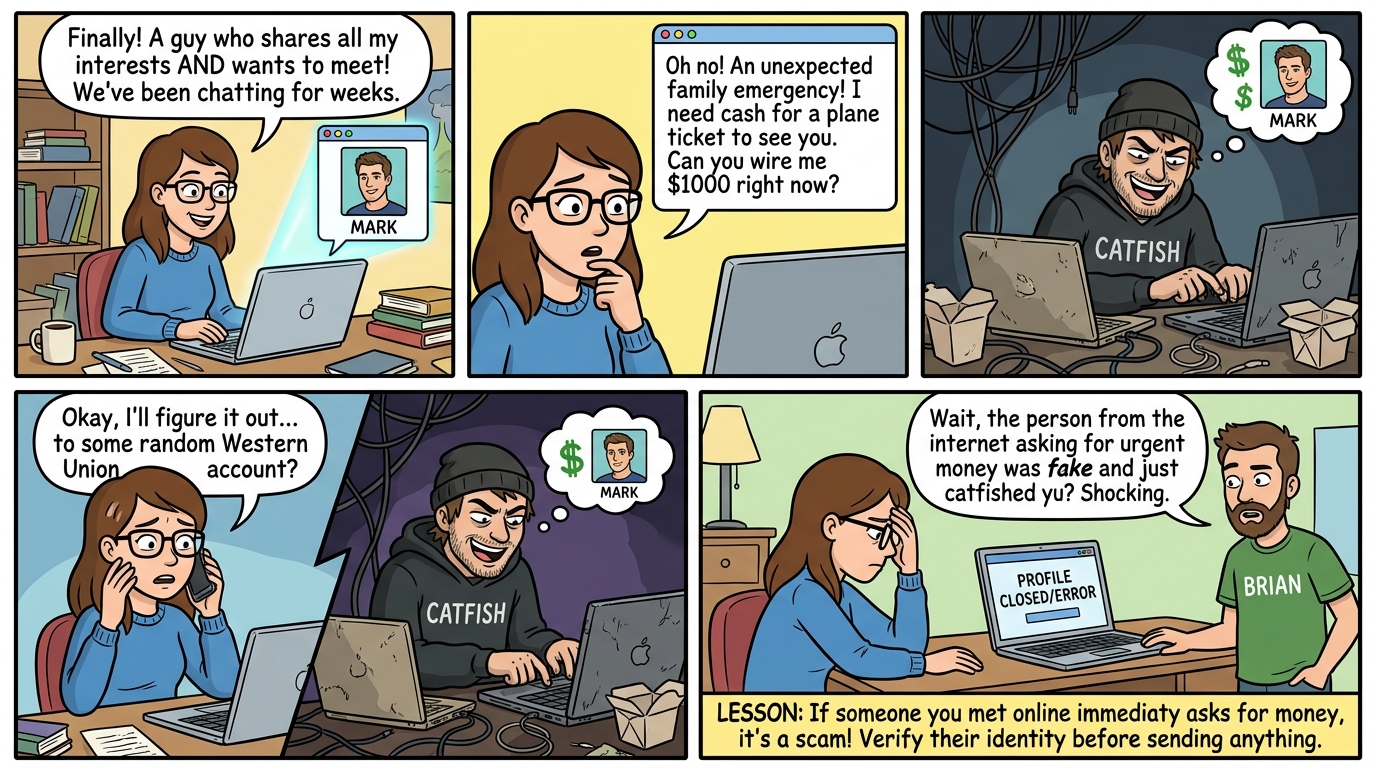
A hacker learns why getting past a password is only half the battle when two-factor authentication s...
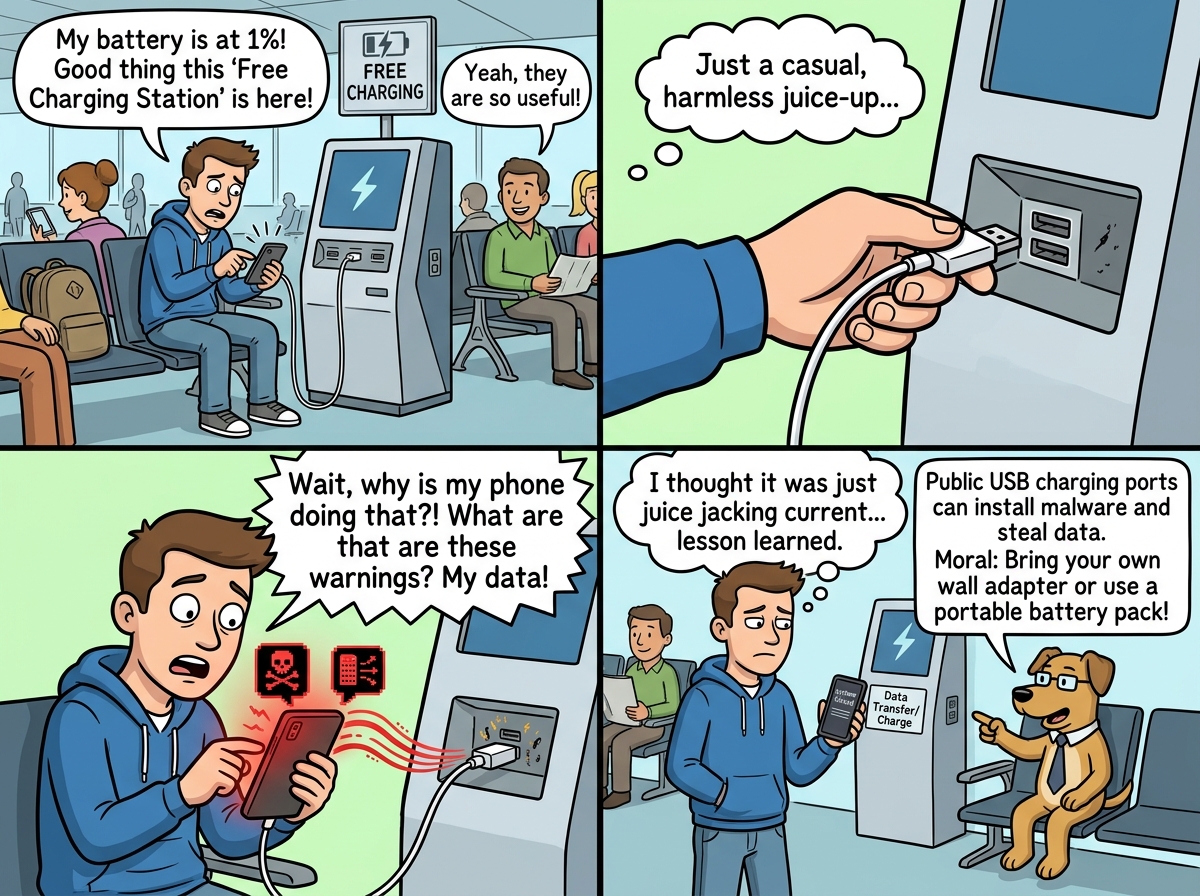
A tired traveler learns the hard way that free airport charging stations can drain more than just ba...

When a data breach hits, panic is NOT a plan. Learn why incident response prep matters before disast...
A sneaky burglar discovers why using the same key for every lock is a terrible idea. Learn how crede...
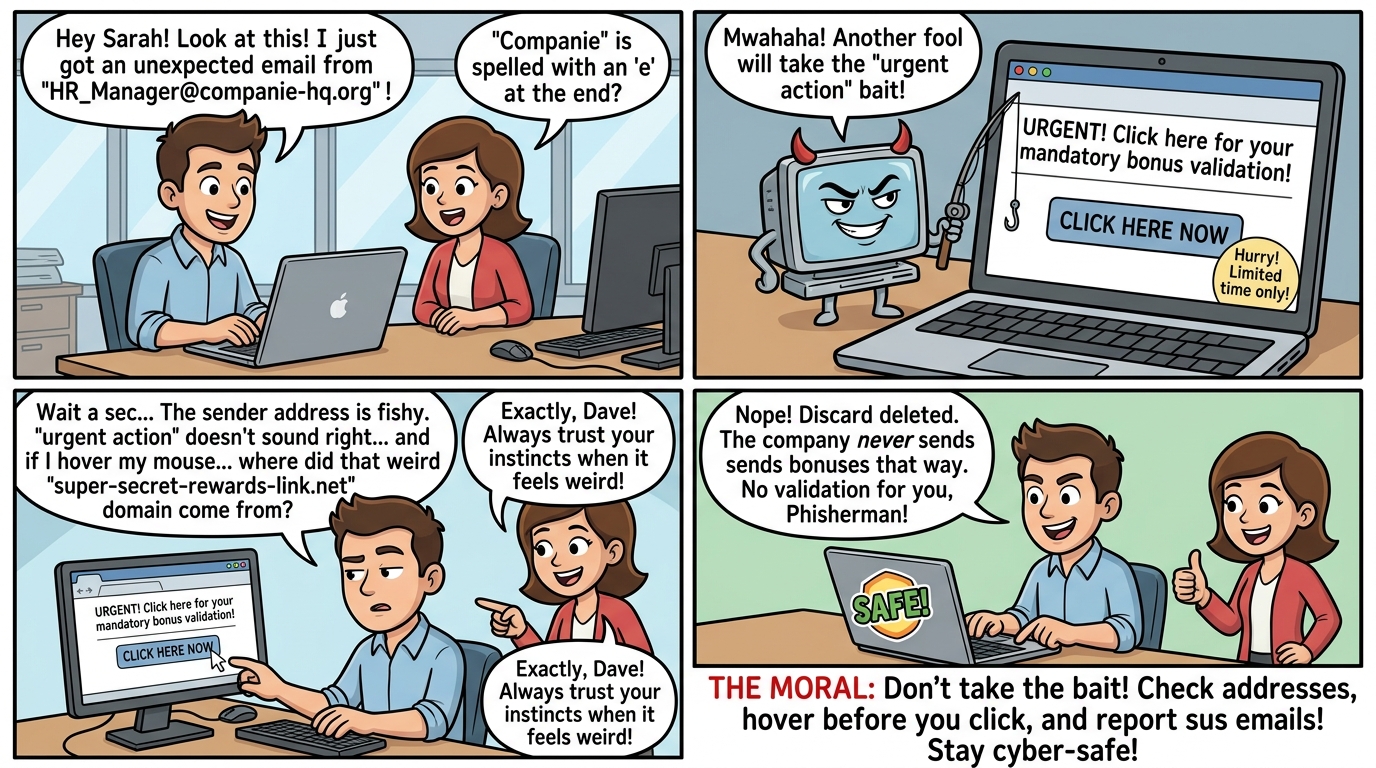
A Nigerian prince's email looks suspicious, but it's the SPELLING that gives him away. Learn to spot...
AI can write phishing emails so perfect they fool even the savvy. Learn how to spot the red flags be...
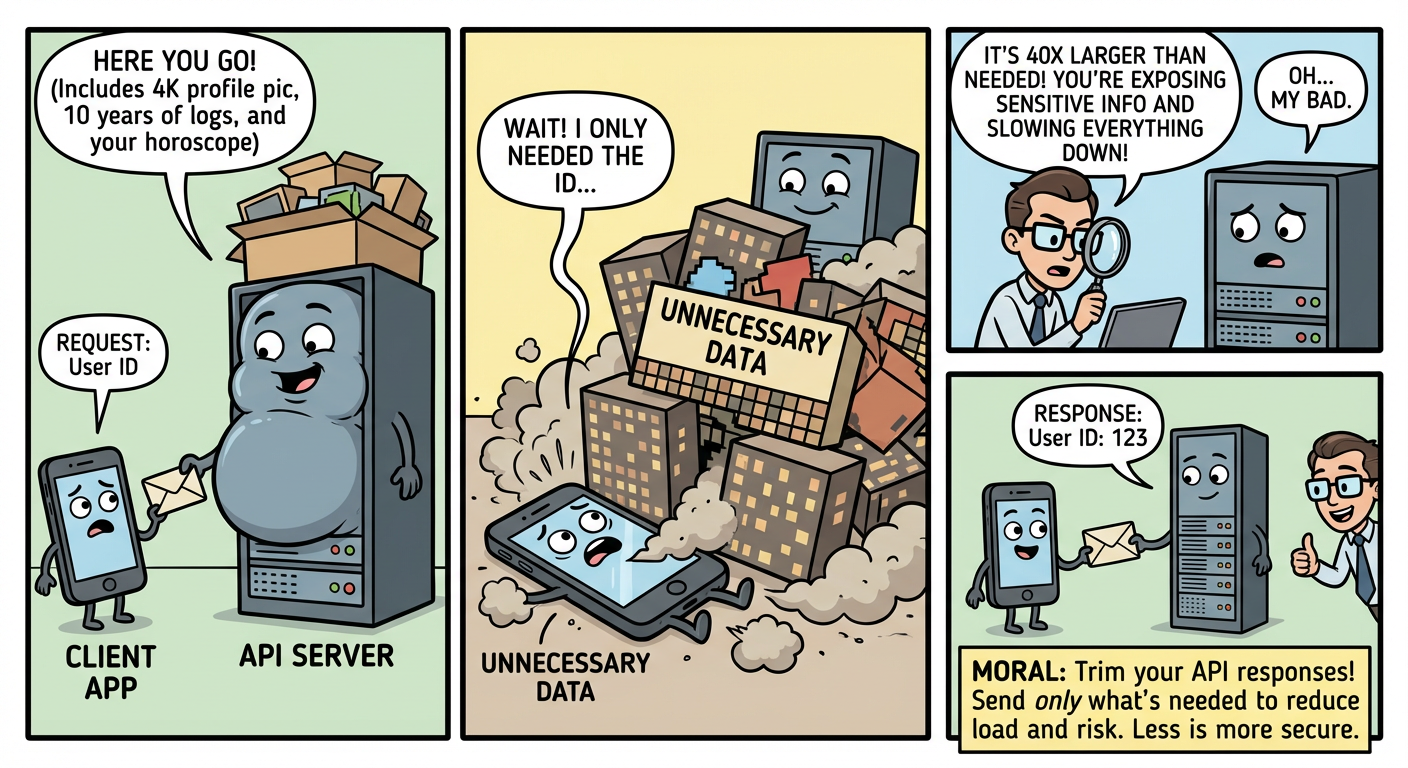
Your API is oversharing like an overeager first date. Learn why bloated responses are a security nig...
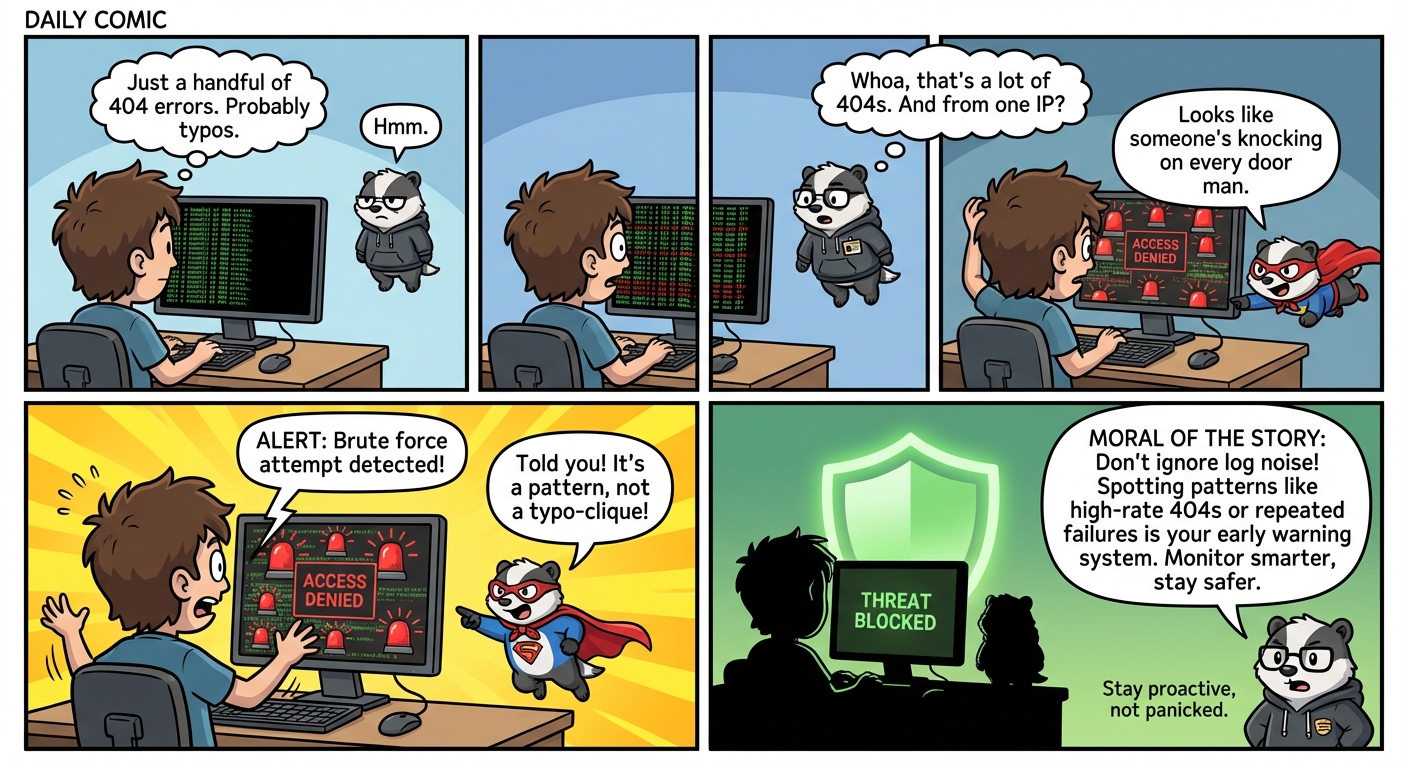
Your server logs are screaming warnings — are you listening? Learn the 5 sneaky patterns that expose...
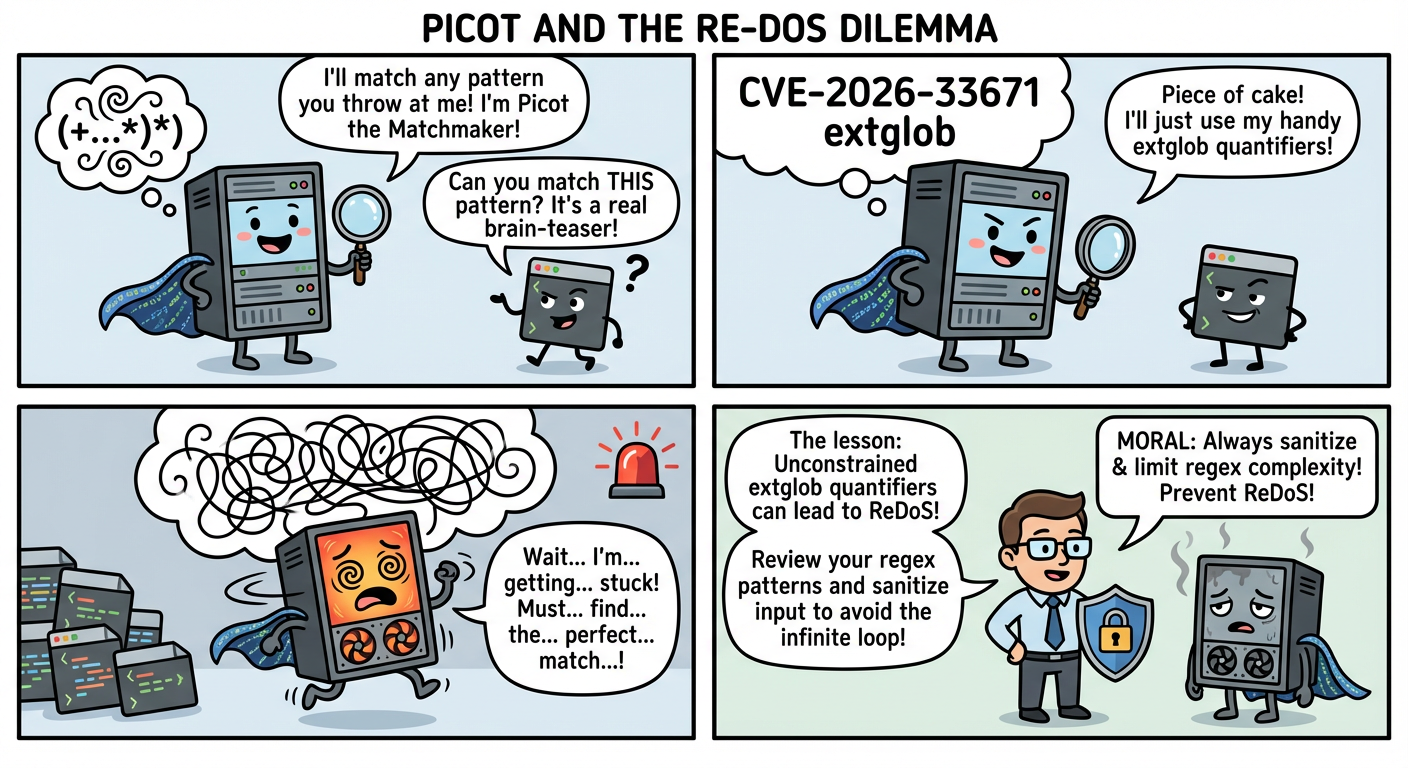
Learn how Regular Expression Denial of Service (ReDoS) attacks can slow systems to a crawl through m...
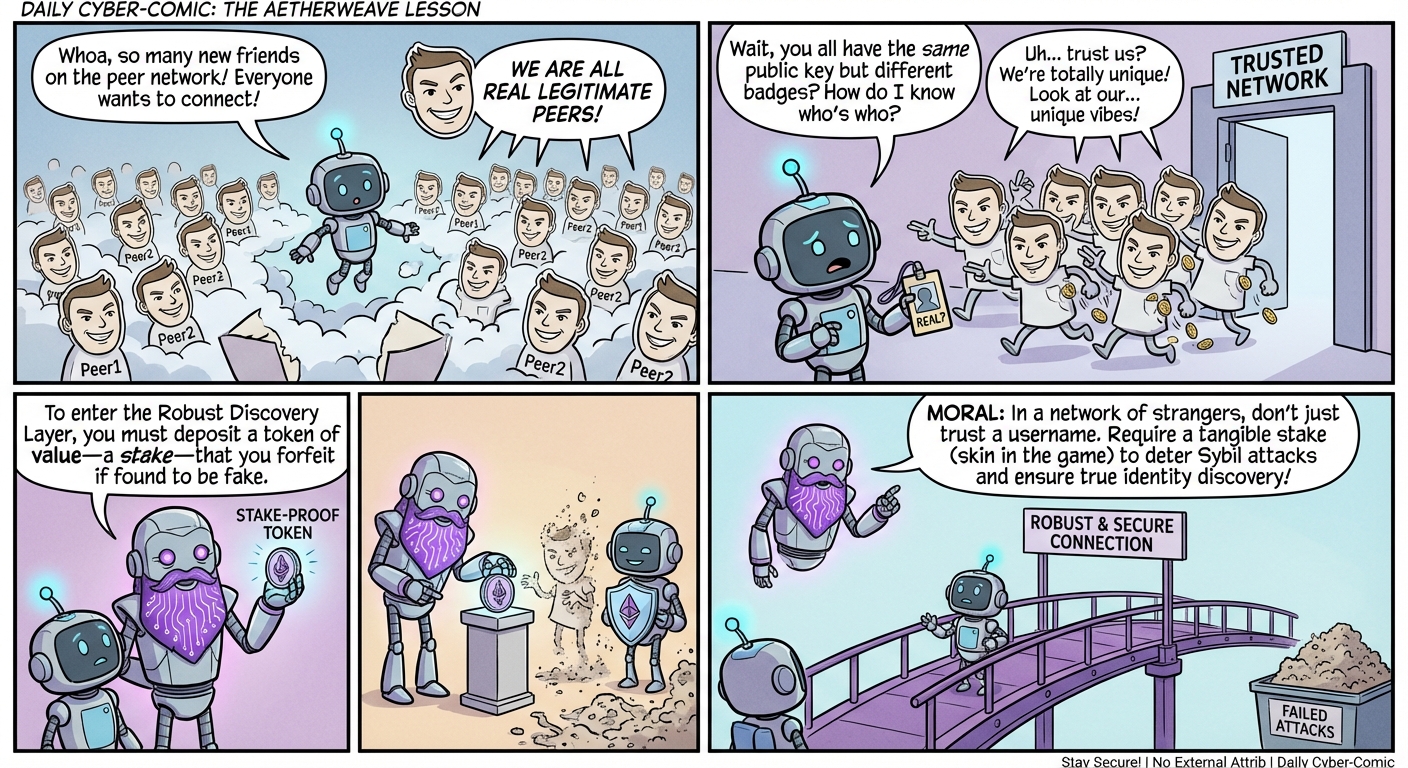
A lighthearted look at how stake-based peer discovery prevents Sybil attacks in decentralized networ...
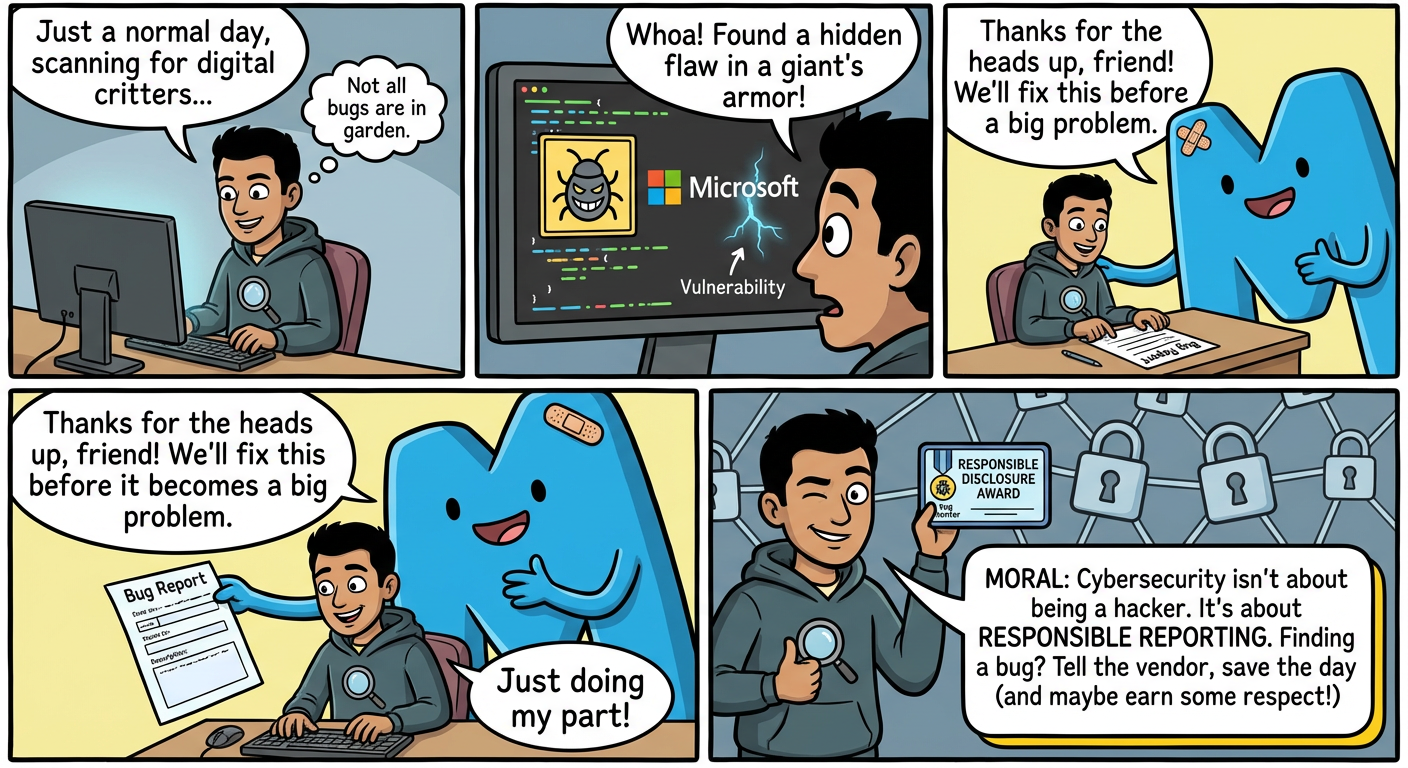
A young security researcher discovers a critical Microsoft vulnerability, showing how ethical hackin...
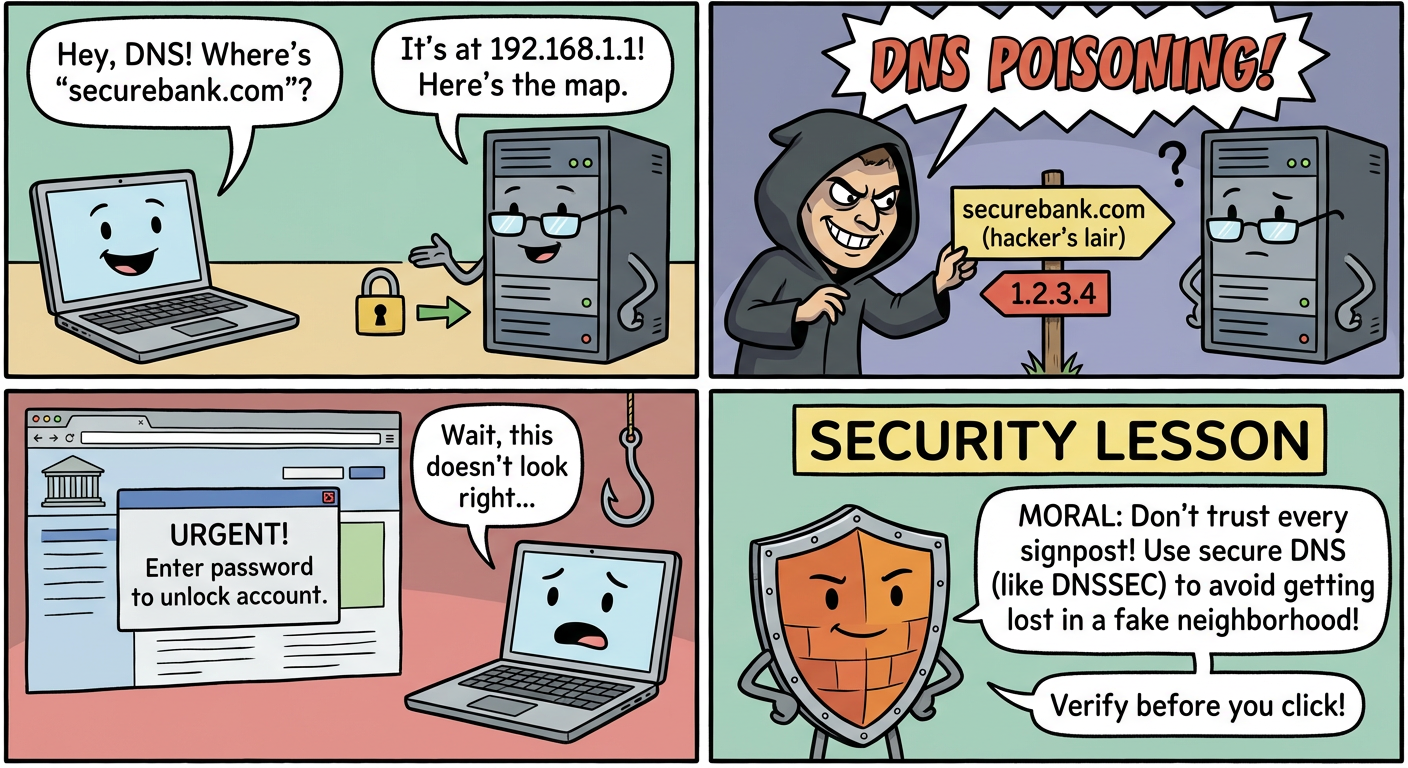
A lighthearted look at how DNS poisoning redirects users to malicious websites, and why checking you...
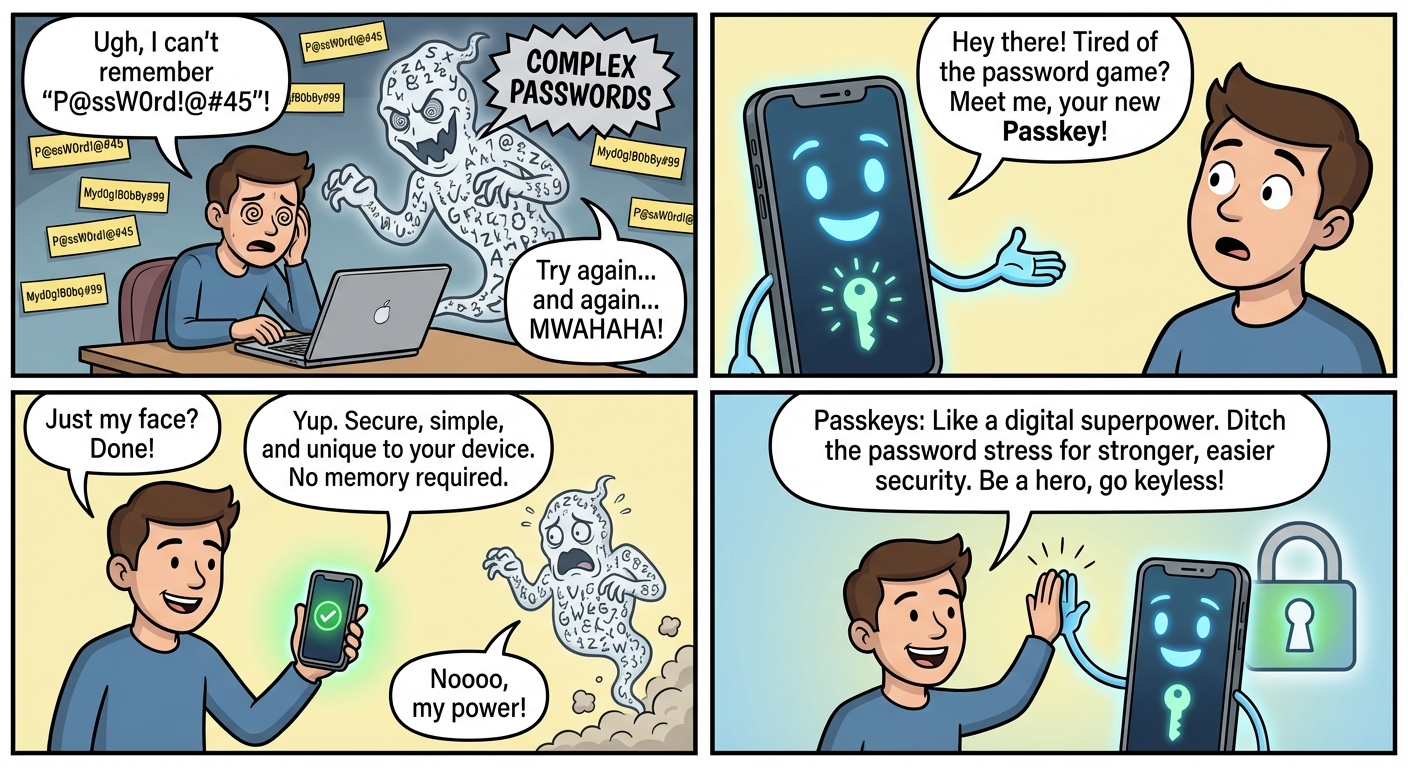
Compare traditional passwords with modern passkeys and discover why passwordless authentication is t...
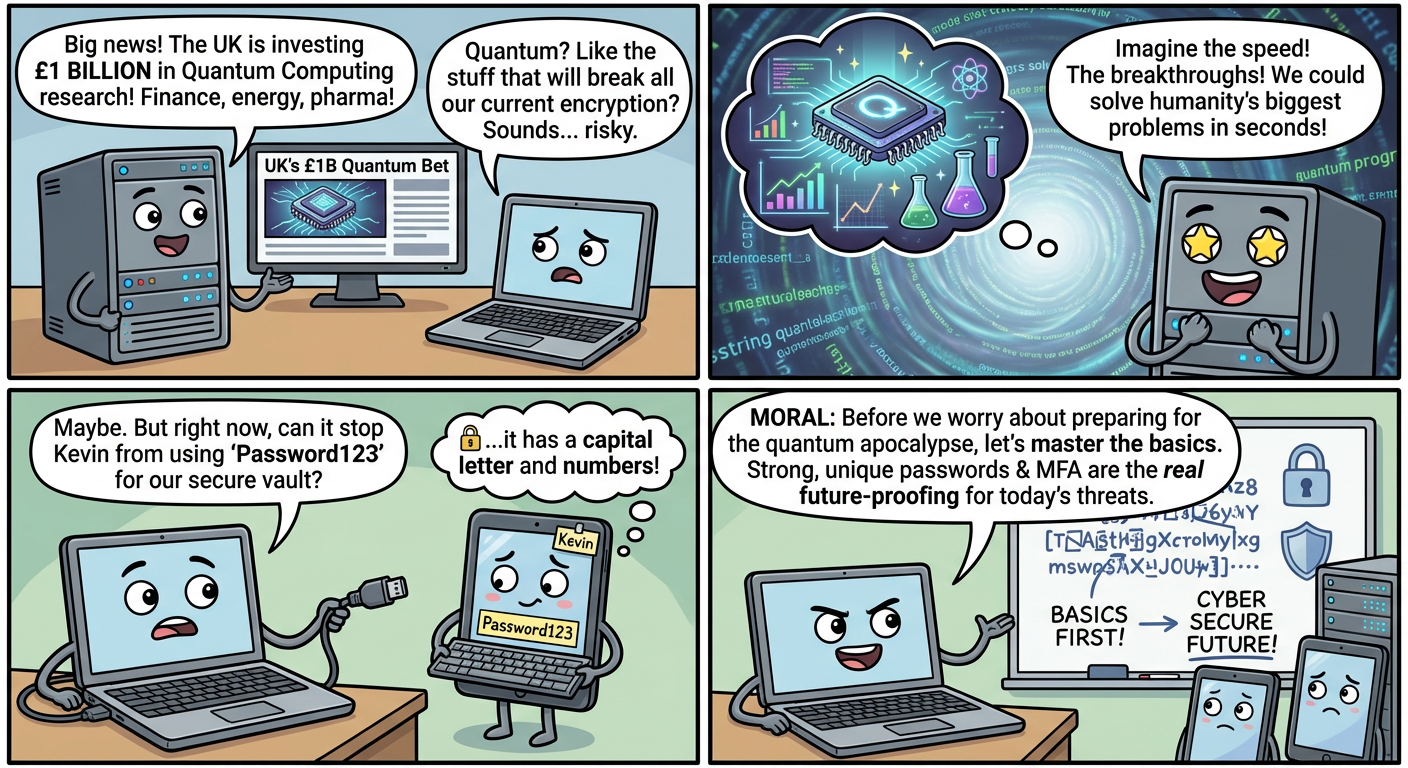
As quantum computing advances, traditional encryption faces new challenges. Learn why quantum-safe s...
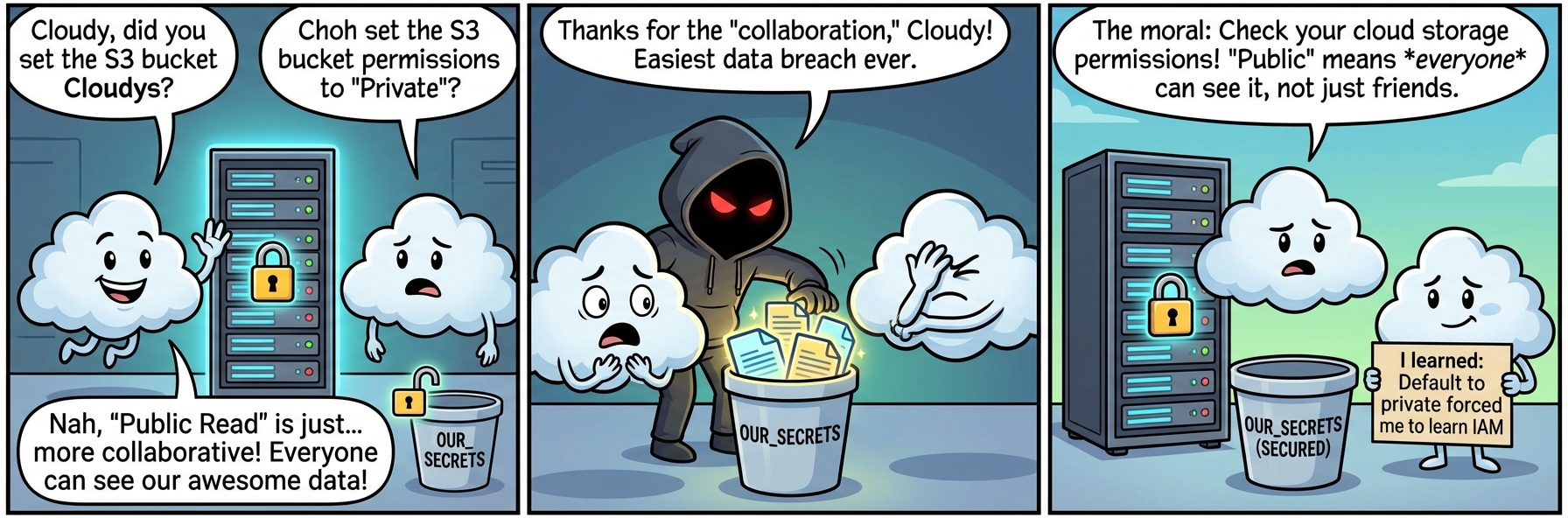
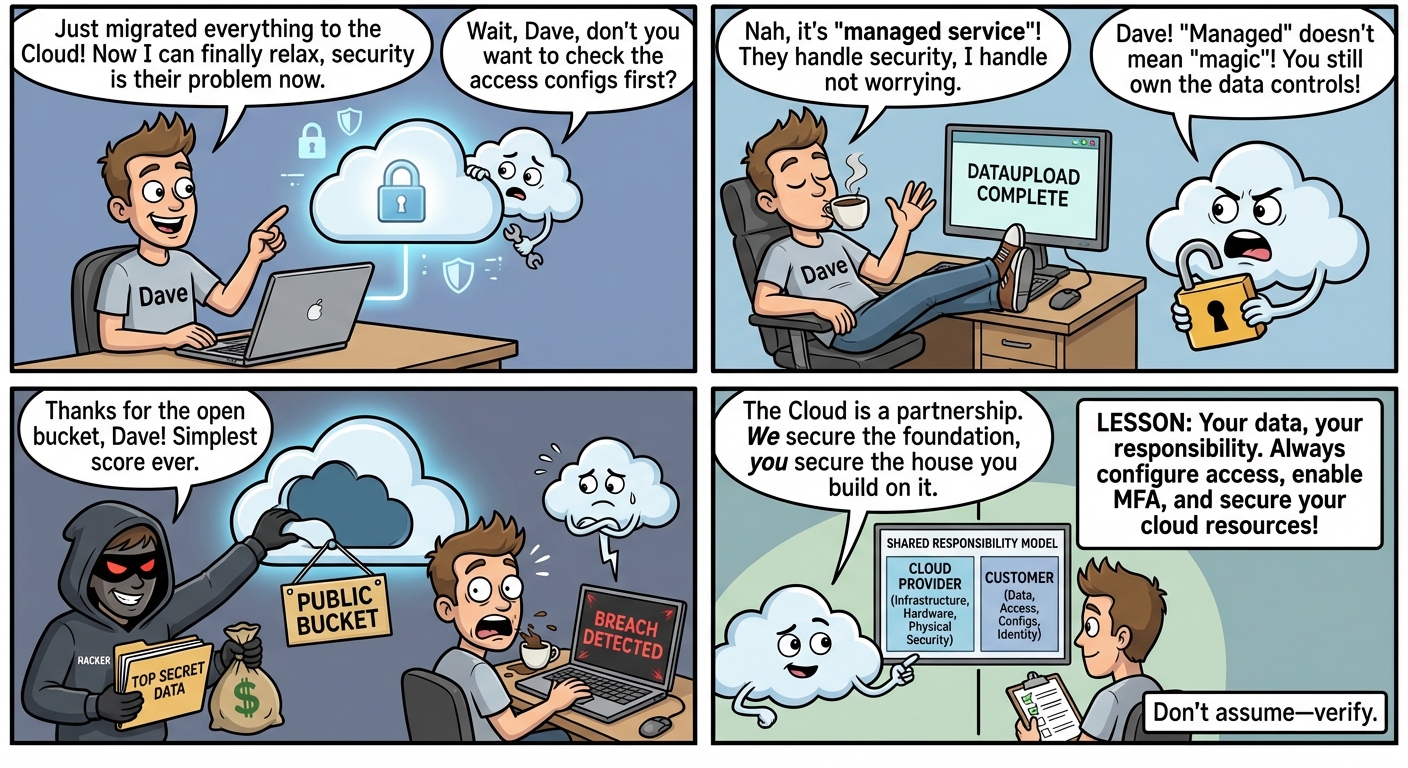
Learn essential cloud security practices through a whimsical journey of a data packet moving between...
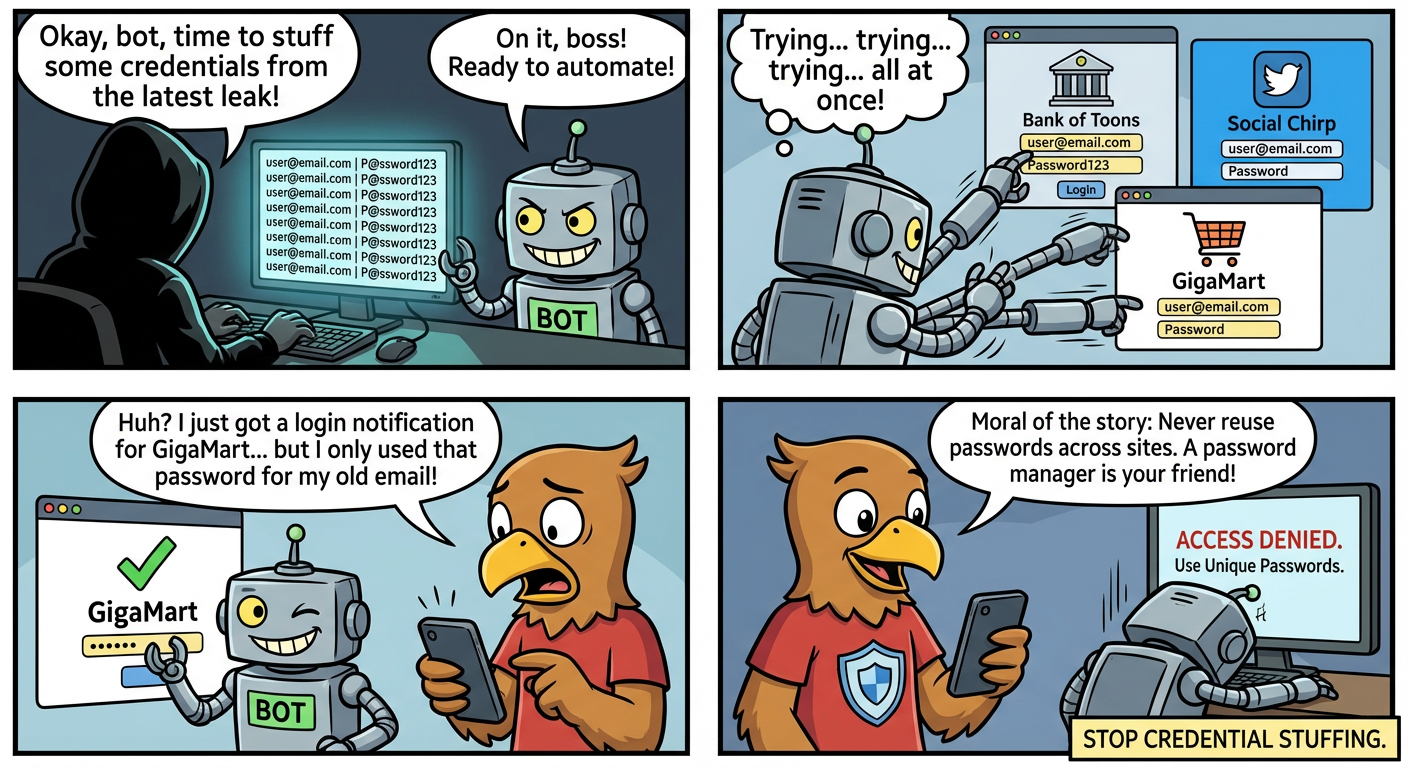
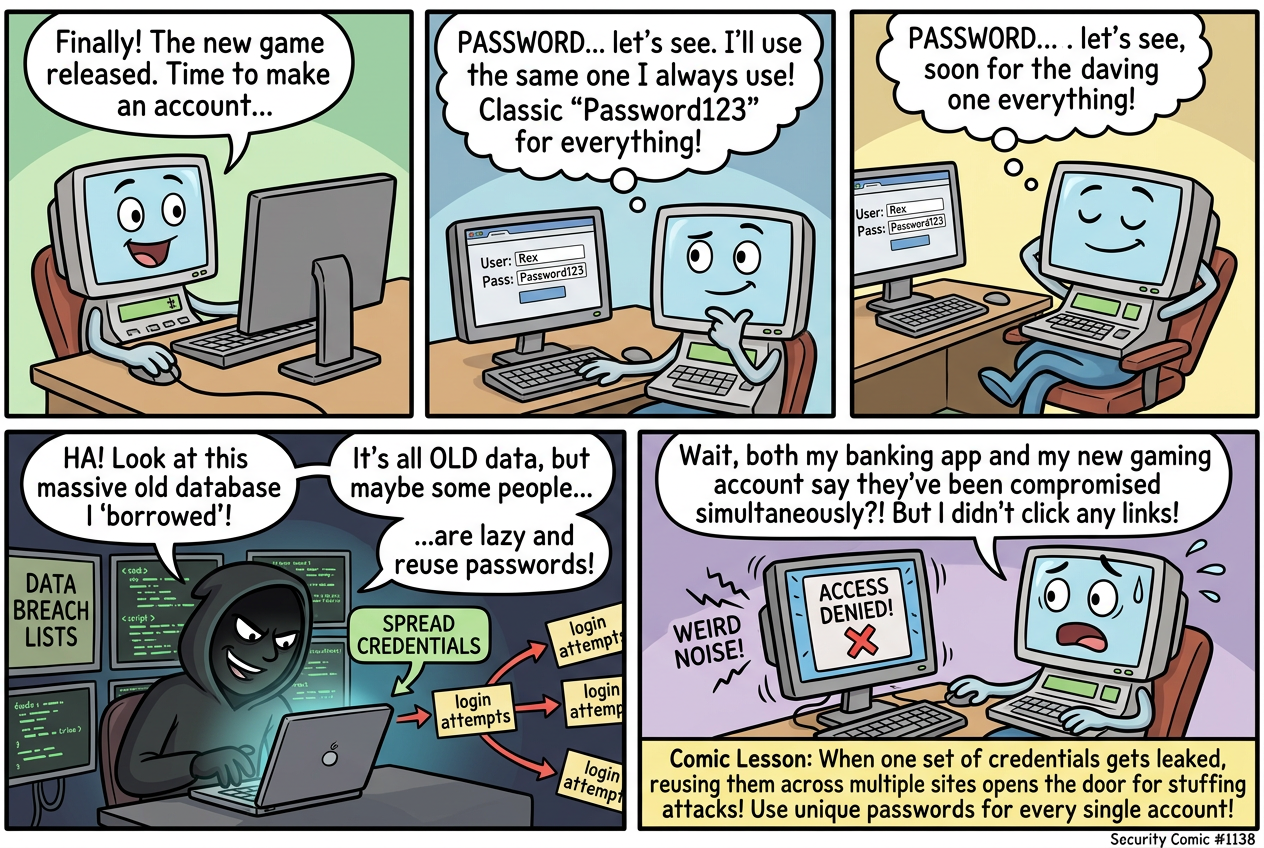
Learn why reusing passwords across multiple sites is dangerous and how credential stuffing attacks c...

A cautionary tale about the dangers of connecting to unsecured public WiFi networks and how hackers ...

Learn how to spot and avoid fake tech support scams that use fear tactics to gain remote access to y...
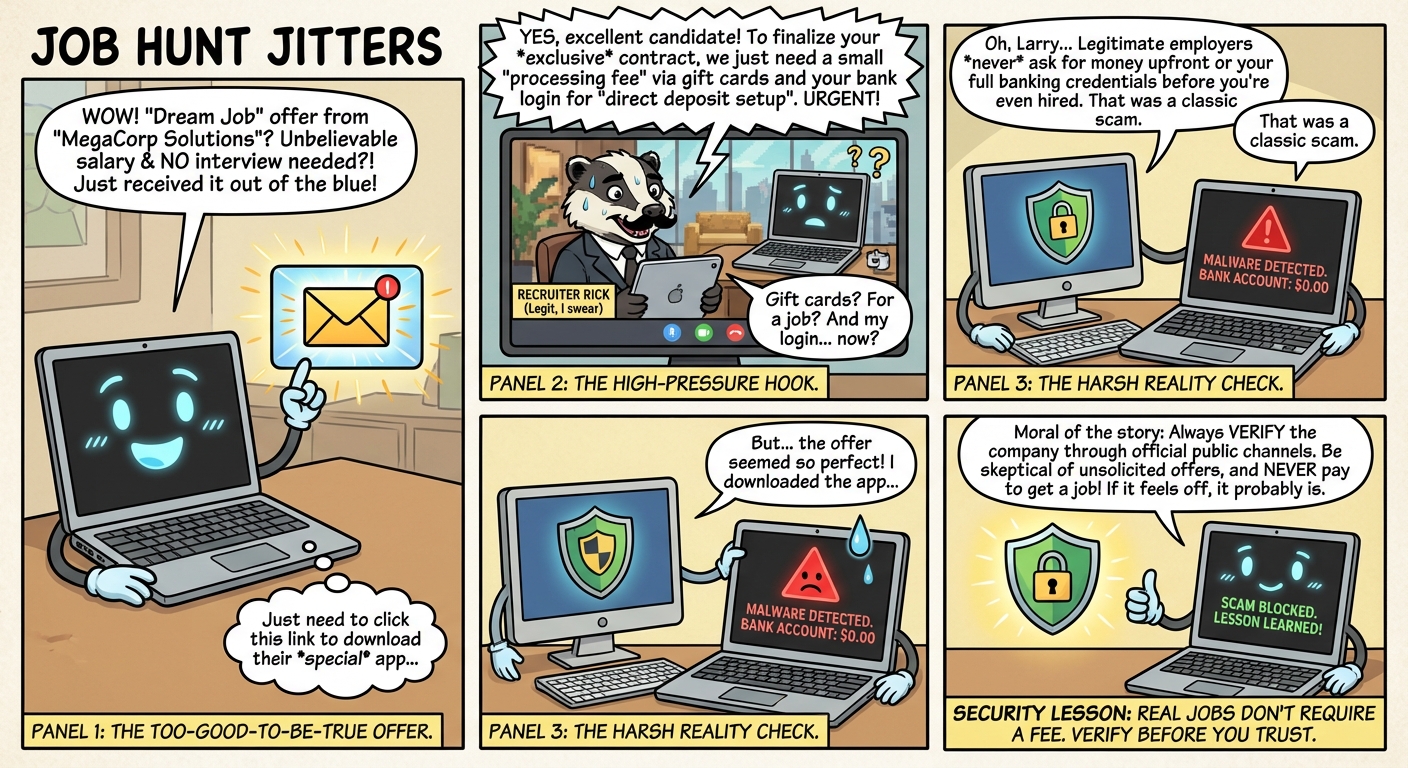
Learn how to spot fake job offer scams and protect yourself from employment fraud schemes targeting ...
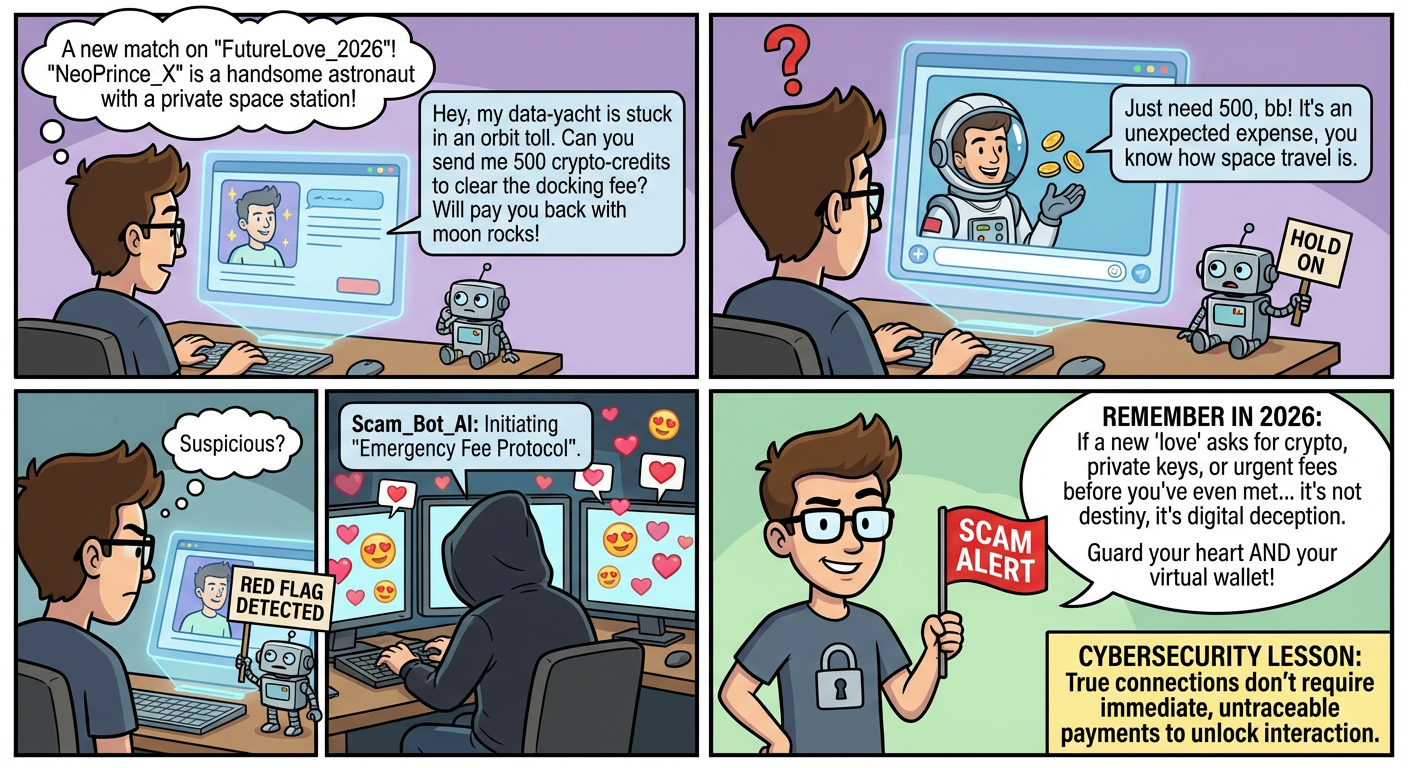
A futuristic look at romance scams in 2026, where AI-powered dating profiles and deep fakes make spo...
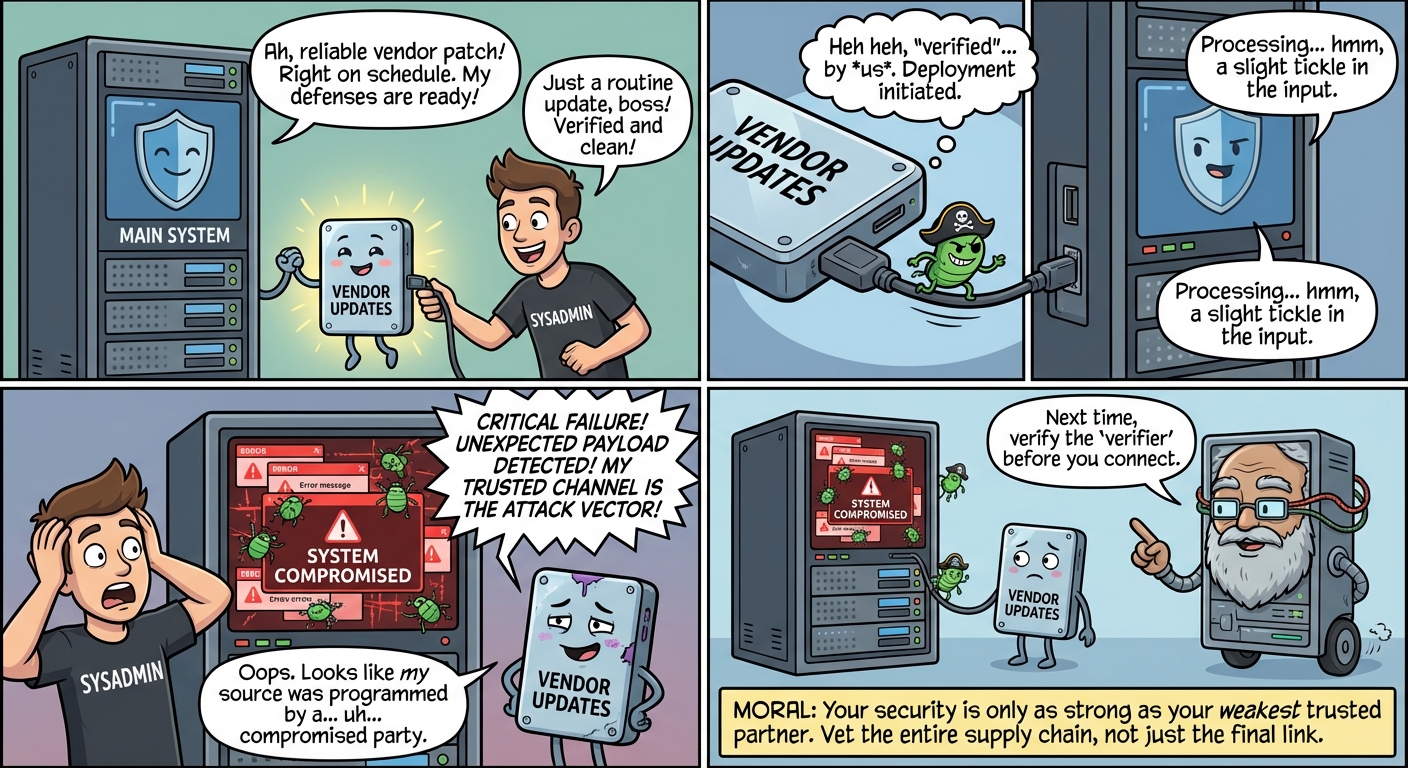
Learn how malicious code can infiltrate trusted software through compromised dependencies and third-...

A humorous look at how amateur radio operators' security mindset and communication protocols can tea...
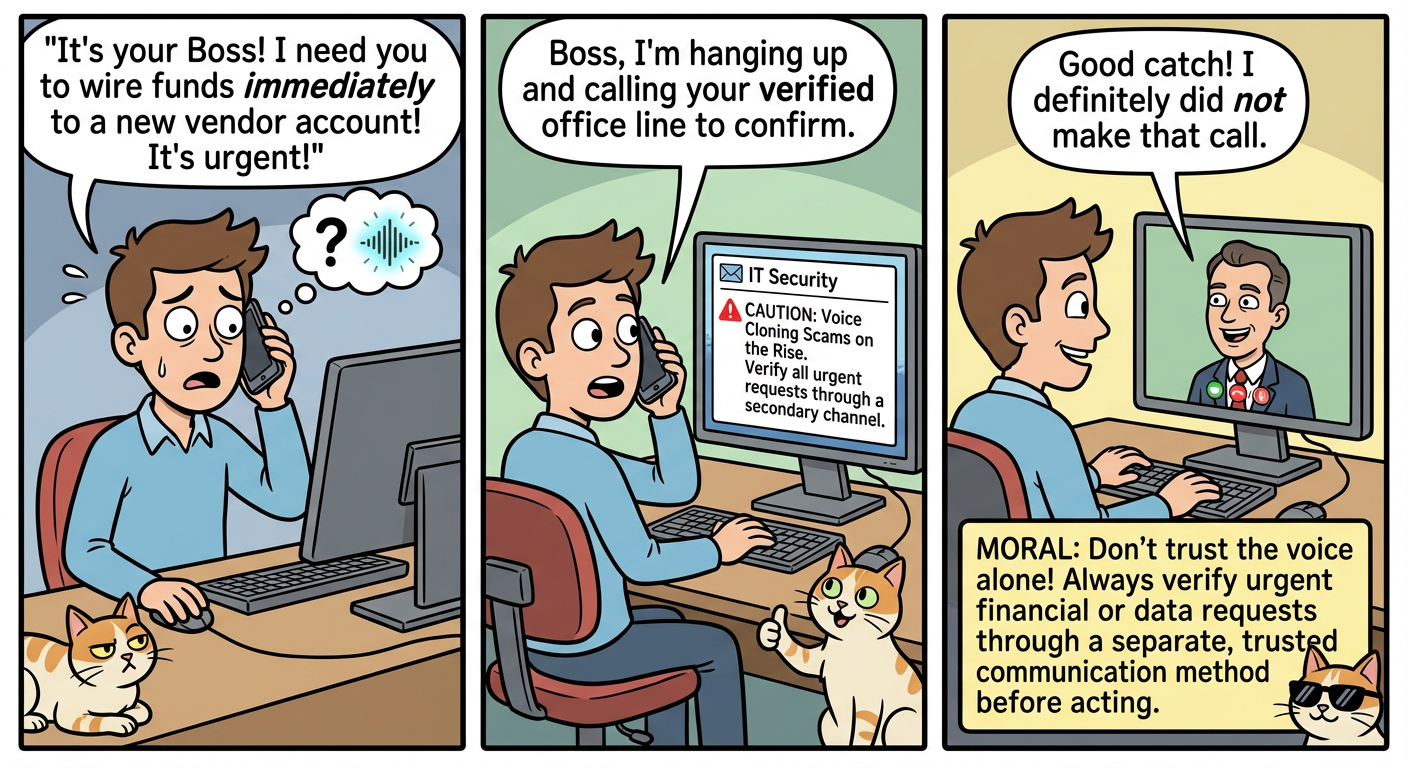
Learn how scammers use AI voice cloning to impersonate loved ones in emergency scams and how to prot...

Don't fall for AI voice scams pretending to be loved ones in distress. Learn how to verify caller id...
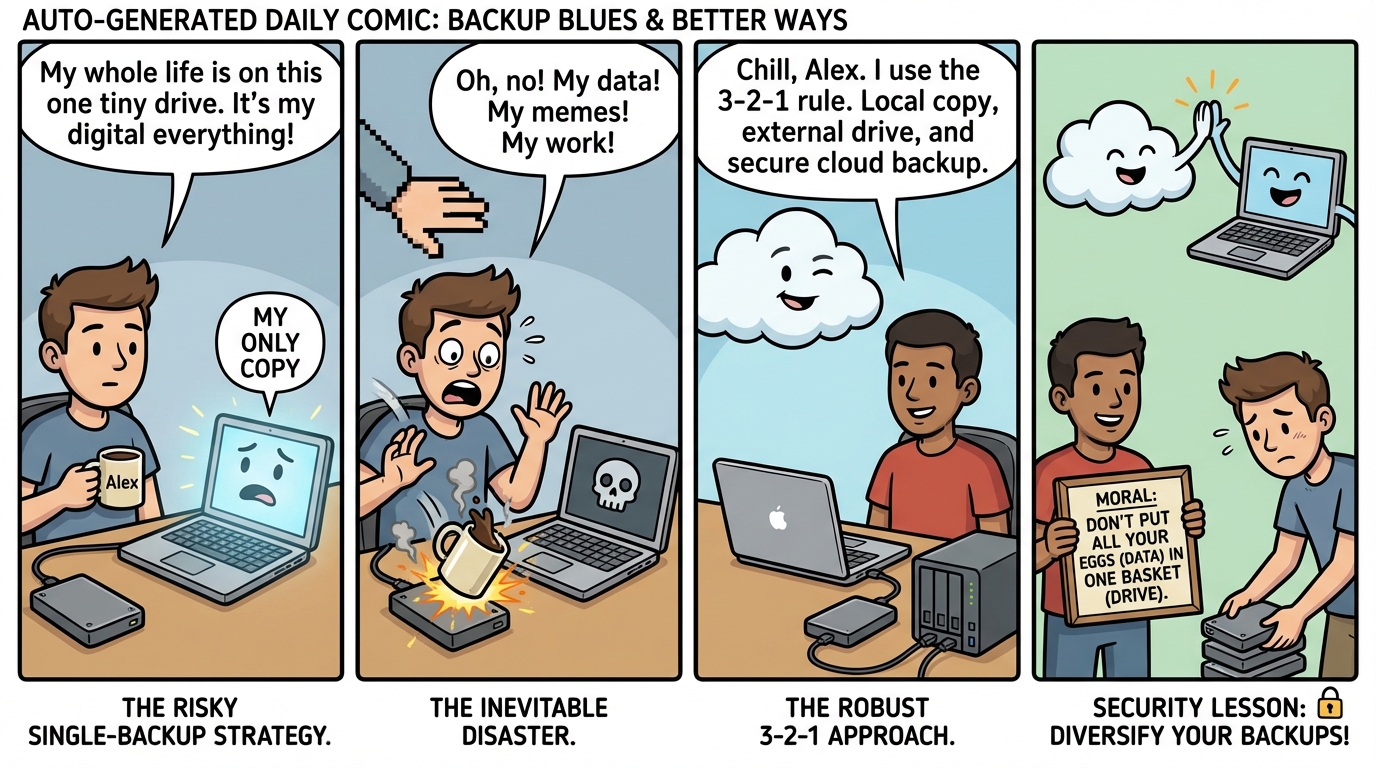
Learn why having multiple backups is crucial through a humorous tale of data disaster and recovery u...
A humorous but eye-opening look at why deleted doesn't mean gone forever in the digital world, and h...
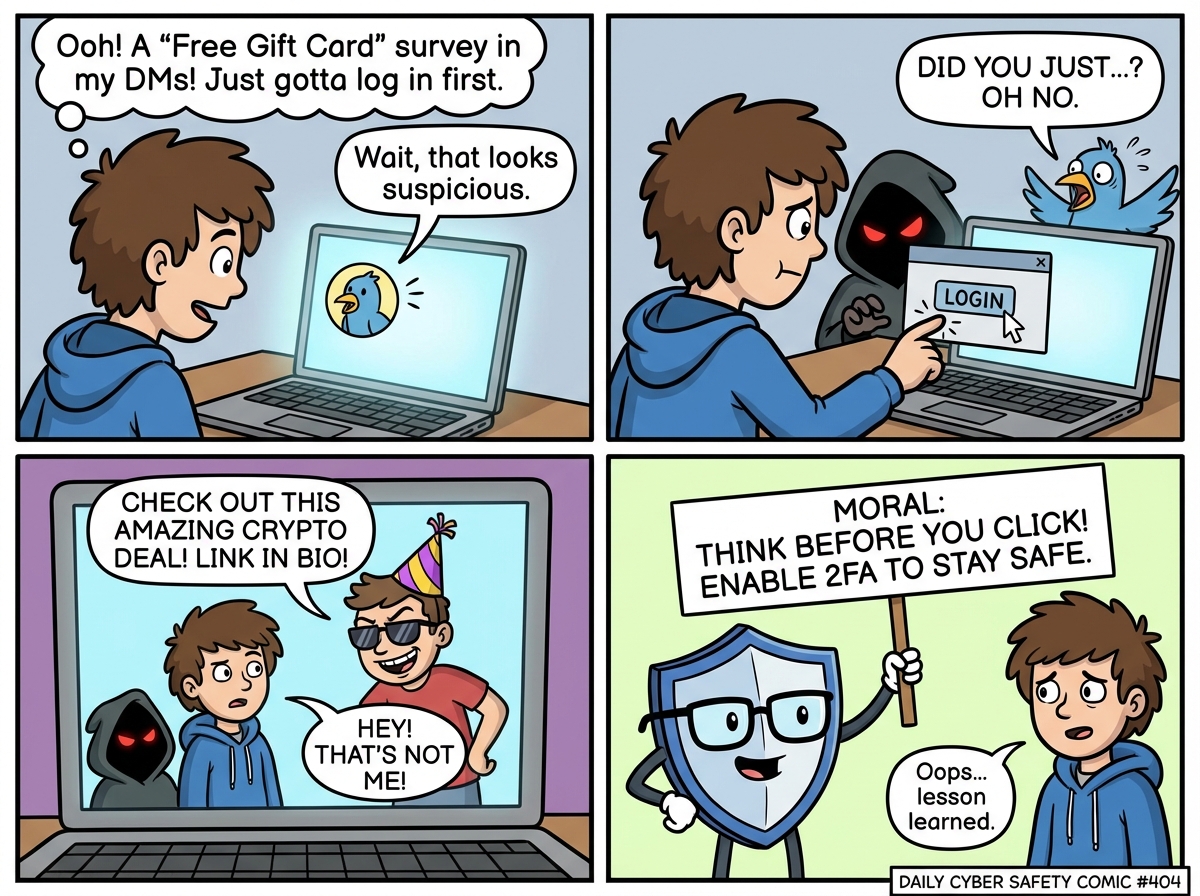
A cautionary tale about the dangers of reusing passwords and ignoring two-factor authentication when...
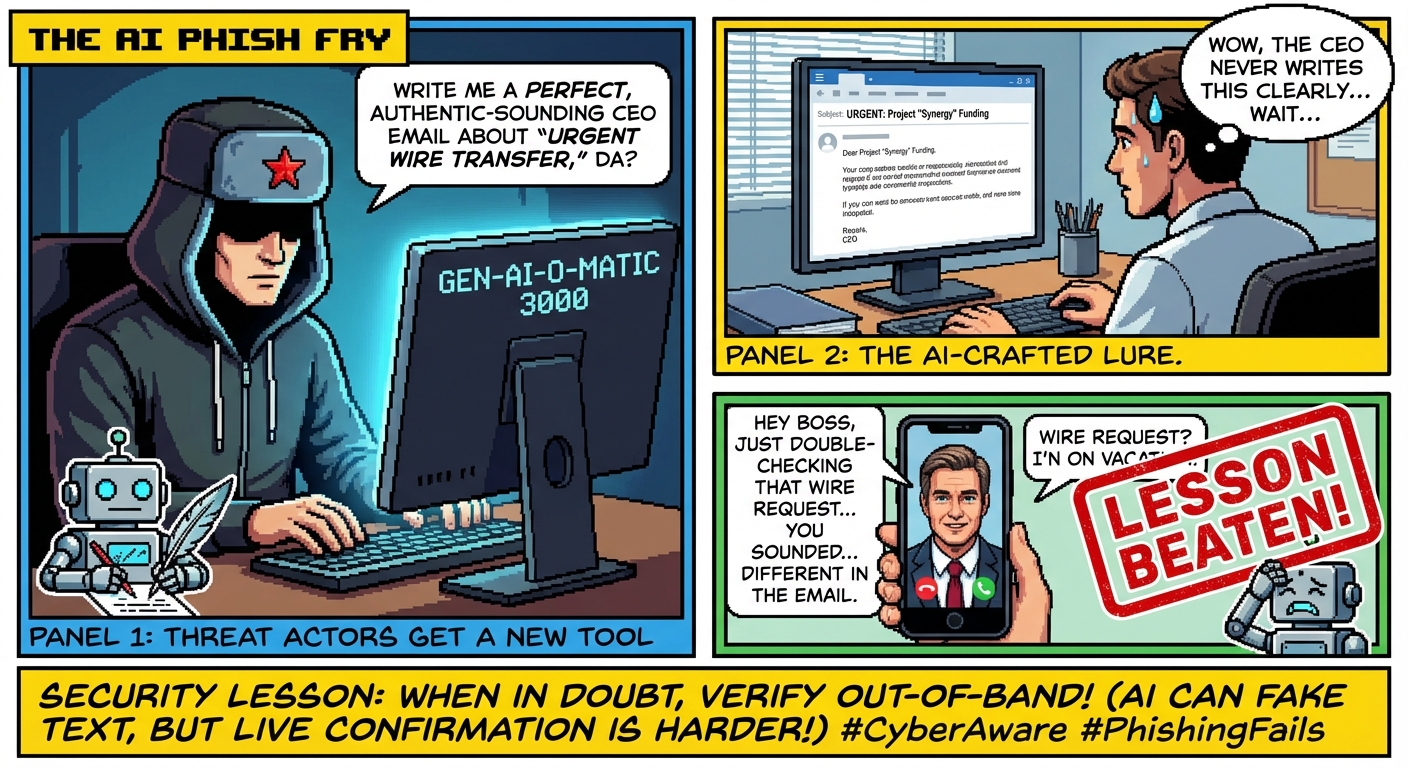
A humorous look at how threat actors leverage AI tools for network intrusion, and why human vigilanc...
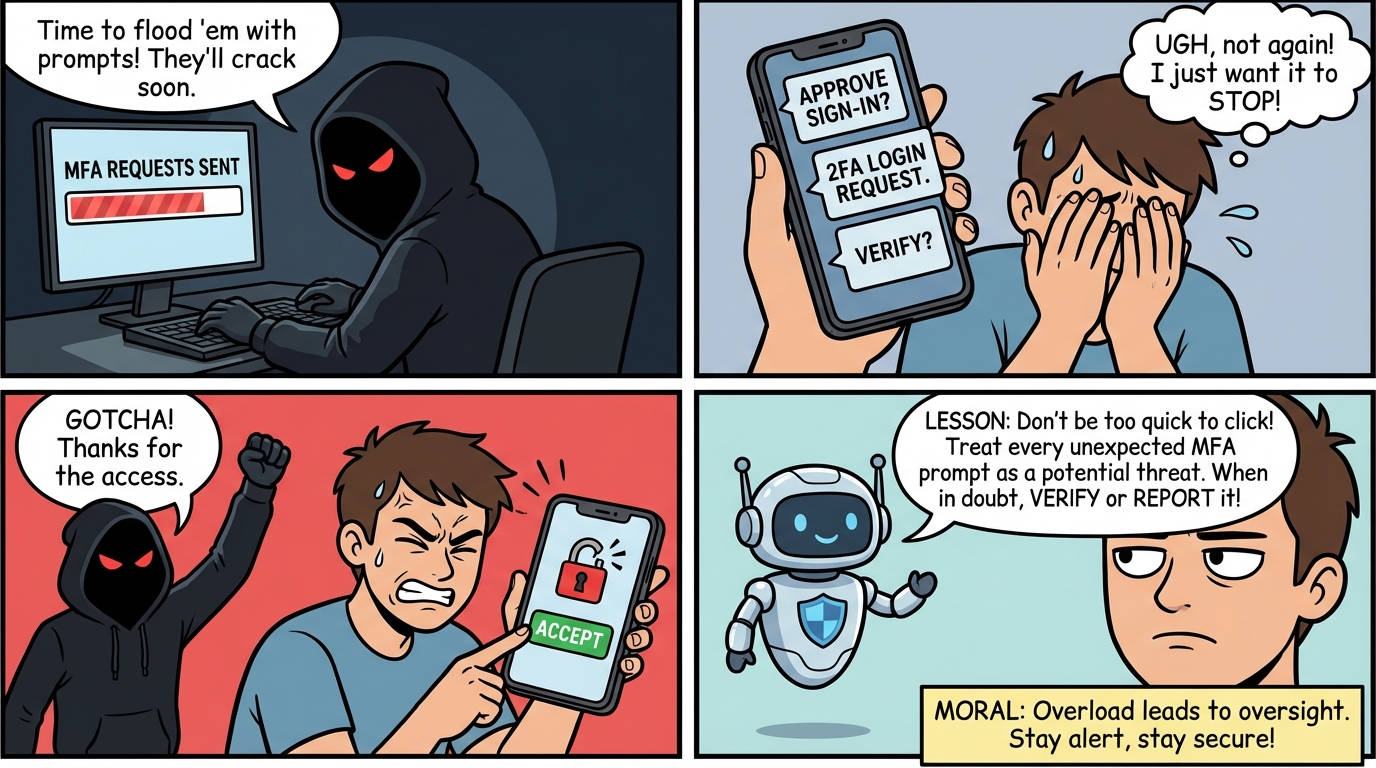
Learn how attackers exploit notification overload to bypass MFA security and what you can do to prot...
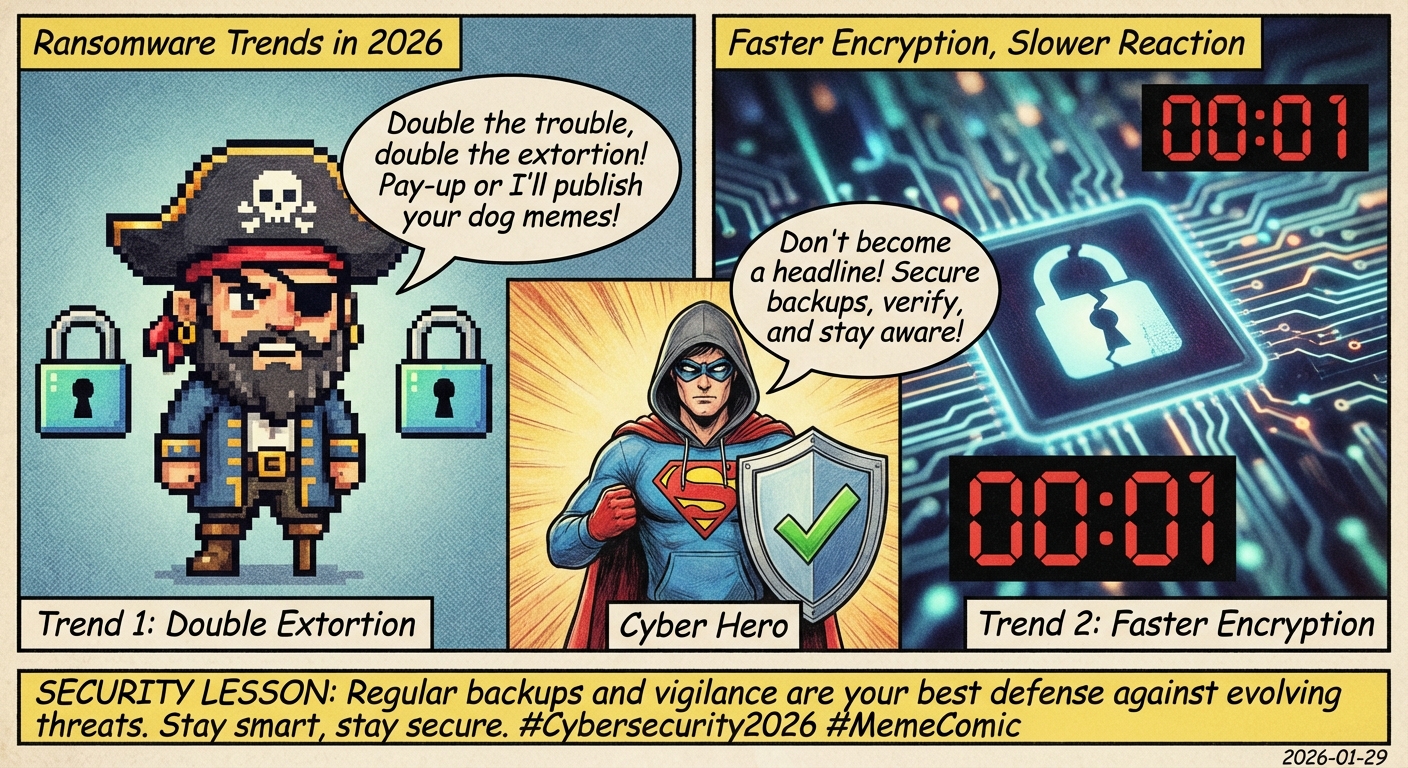
Future ransomware attackers don't just encrypt - they steal and expose data too! Learn how double ex...

Learn how AI-powered attacks breached 600+ firewalls globally, highlighting the importance of keepin...
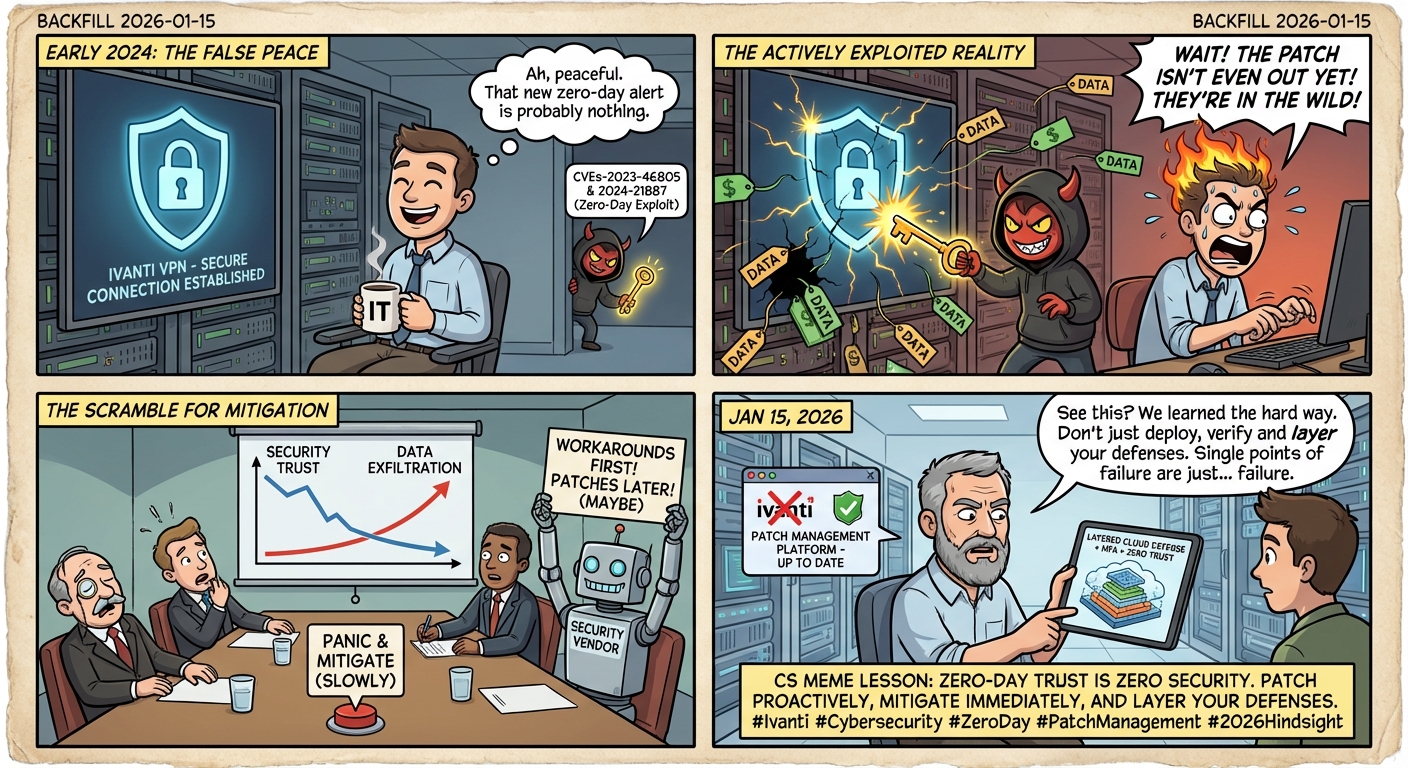
A humorous take on the critical Ivanti VPN vulnerability, showing why keeping security systems updat...
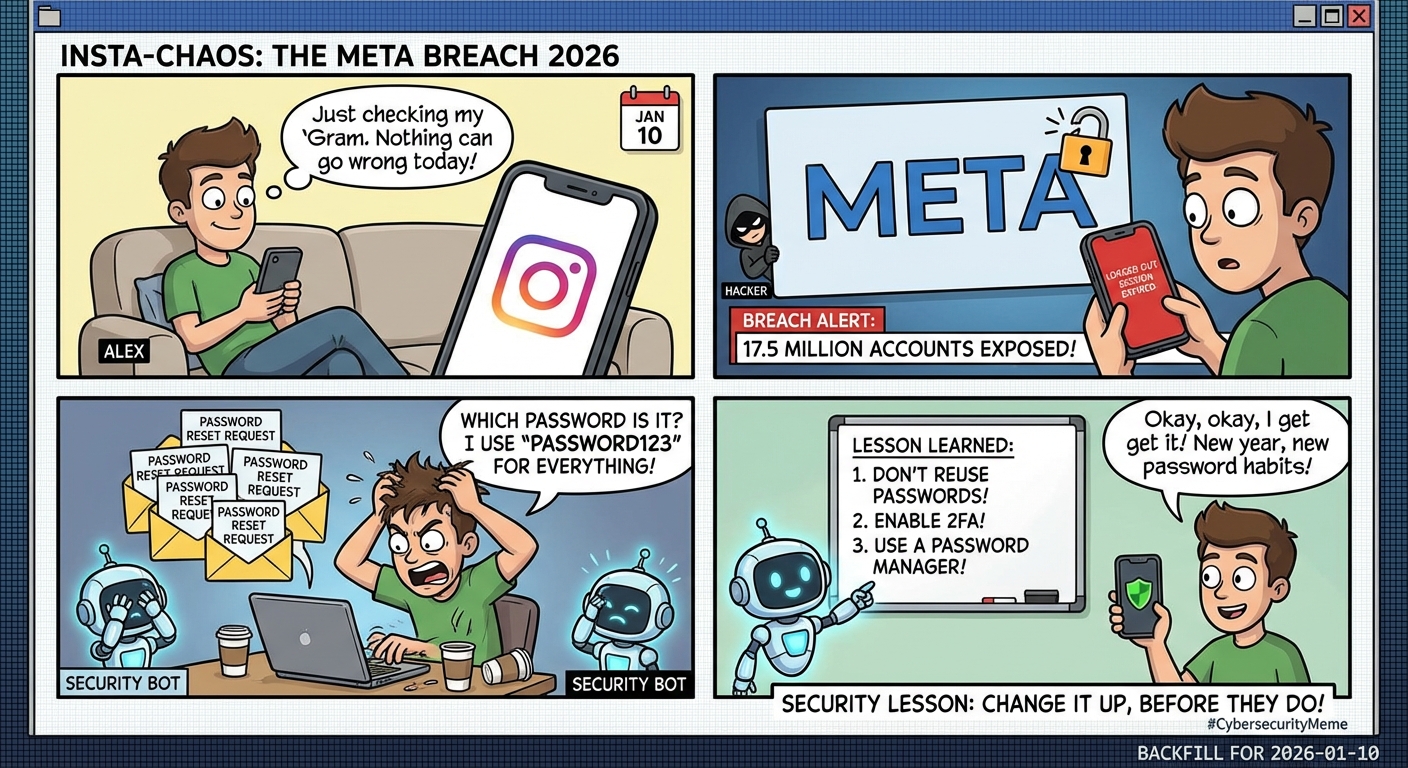
When 17.5M Instagram accounts got breached, chaos ensued. Learn why strong, unique passwords and 2FA...
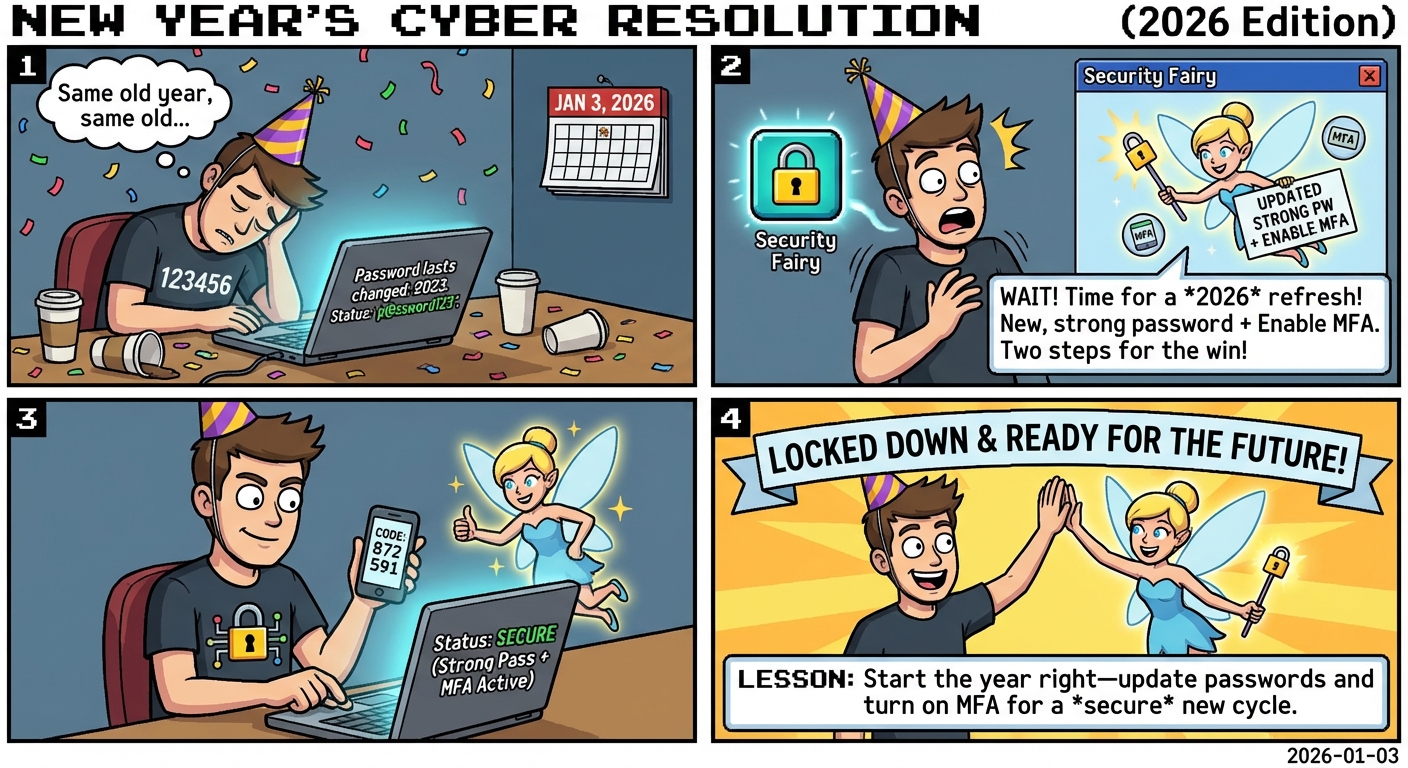
Start 2026 right with strong password hygiene! Follow our cybersecurity penguin as he learns about p...
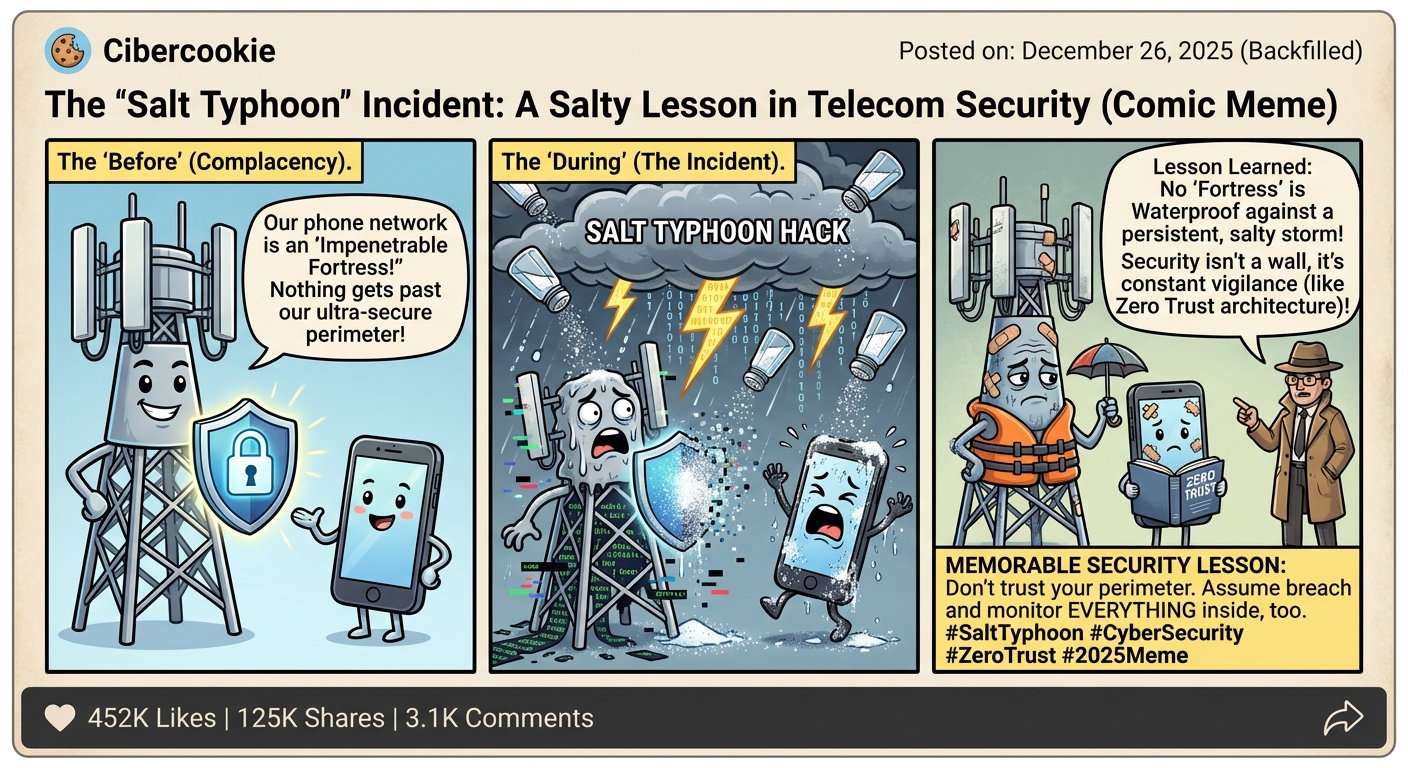
A satirical look at the Salt Typhoon telecom hack that exposed vulnerabilities in US phone networks ...

How EU's Digital Services Act fights tech addiction by banning manipulative design features targetin...

A real-world cautionary tale about how a single compromised third-party widget led to massive data b...

Discover how social engineers bypass technical security through psychological manipulation. A crucia...

A humorous but cautionary tale about the real consequences of postponing software updates, and how p...
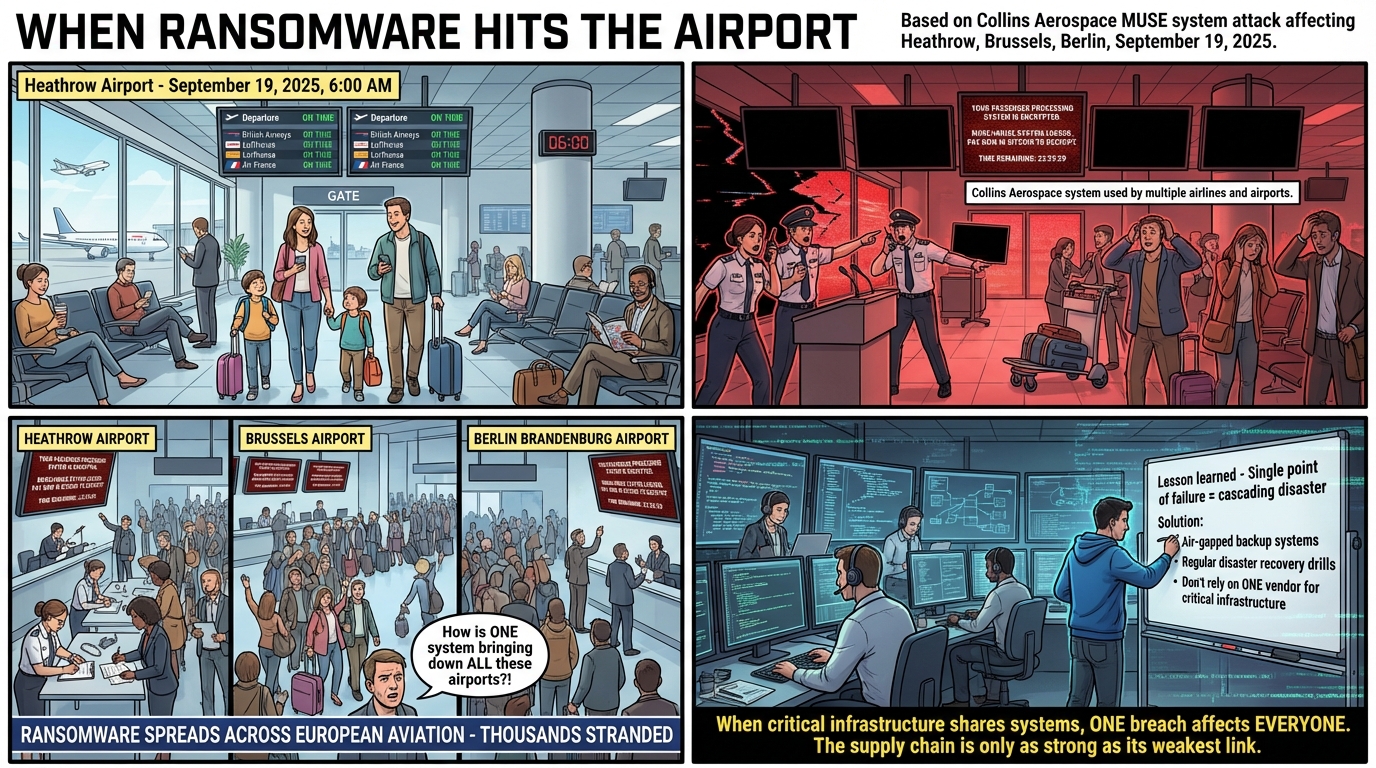
A real-world lesson on supply chain vulnerabilities and shared infrastructure risks. When critical s...

A humorous look at how tracking cookies follow your online activity, and why managing cookie permiss...
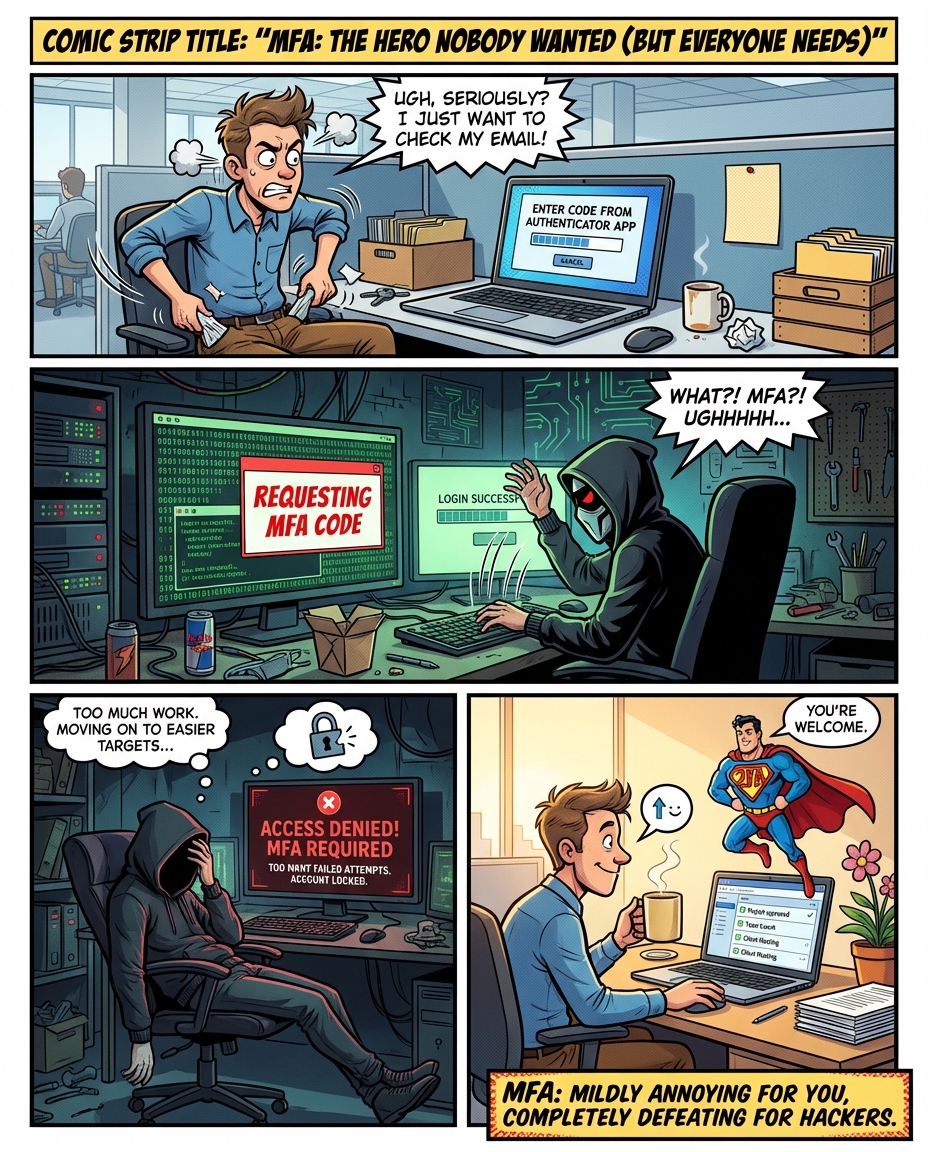
Discover how Multi-Factor Authentication, though slightly inconvenient, effectively blocks 99.9% of ...
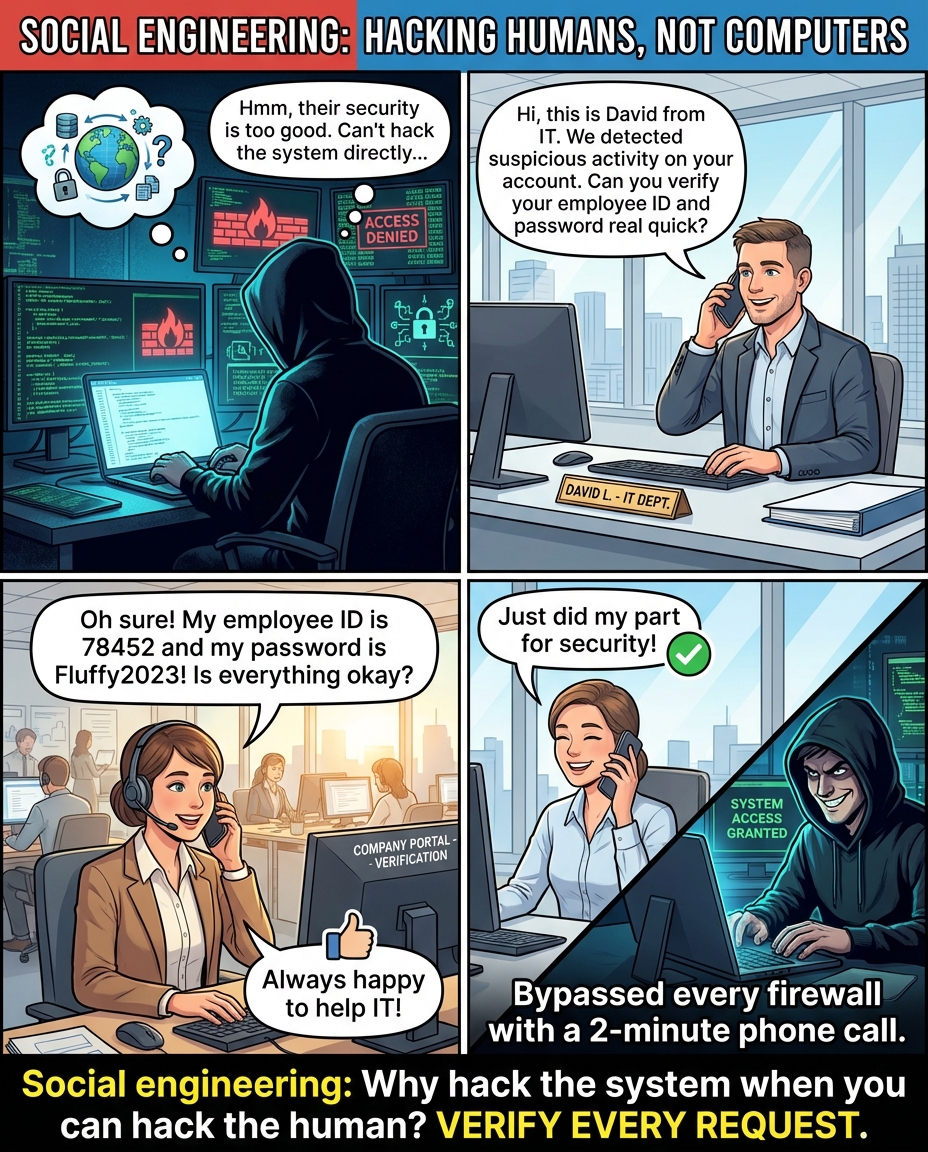
A cautionary tale about social engineering showing how hackers bypass technical security through hum...
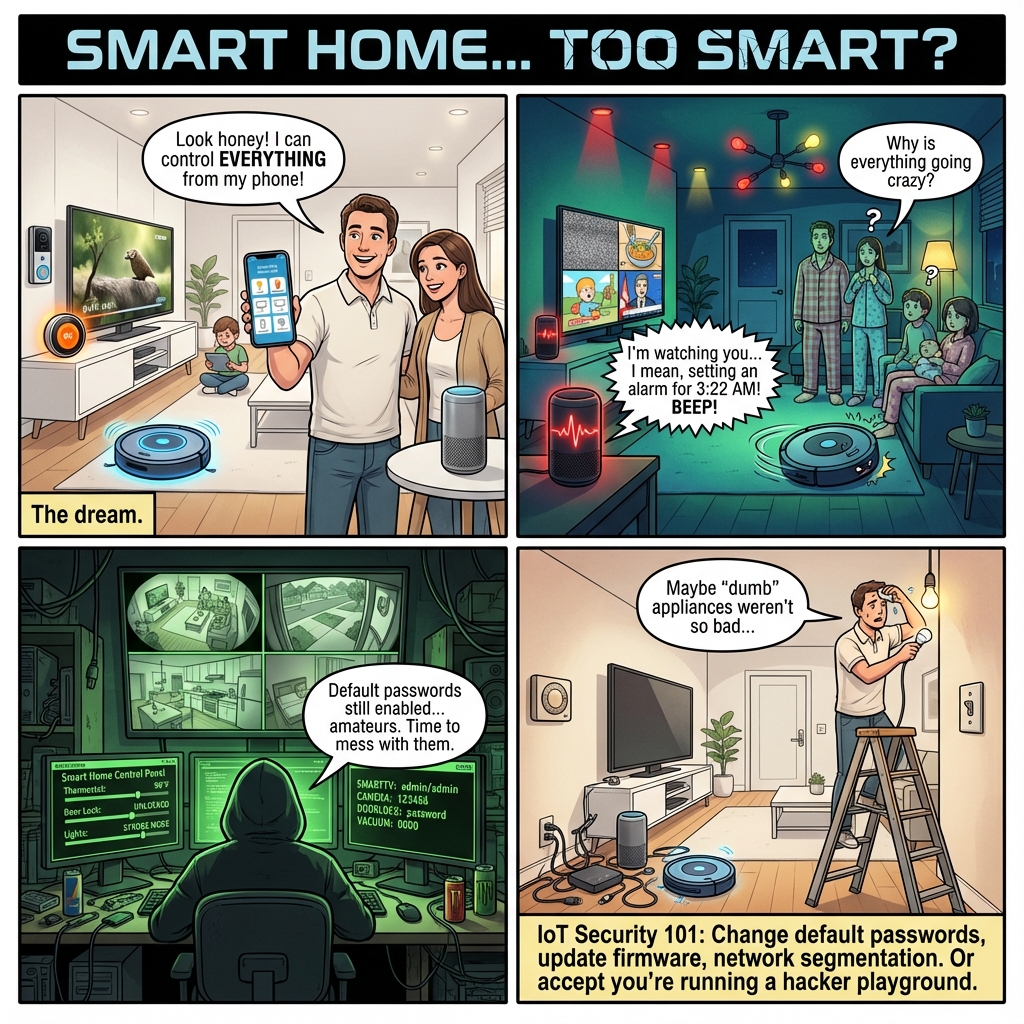
A family learns the hard way why default passwords and unsecured IoT devices can turn their dream sm...
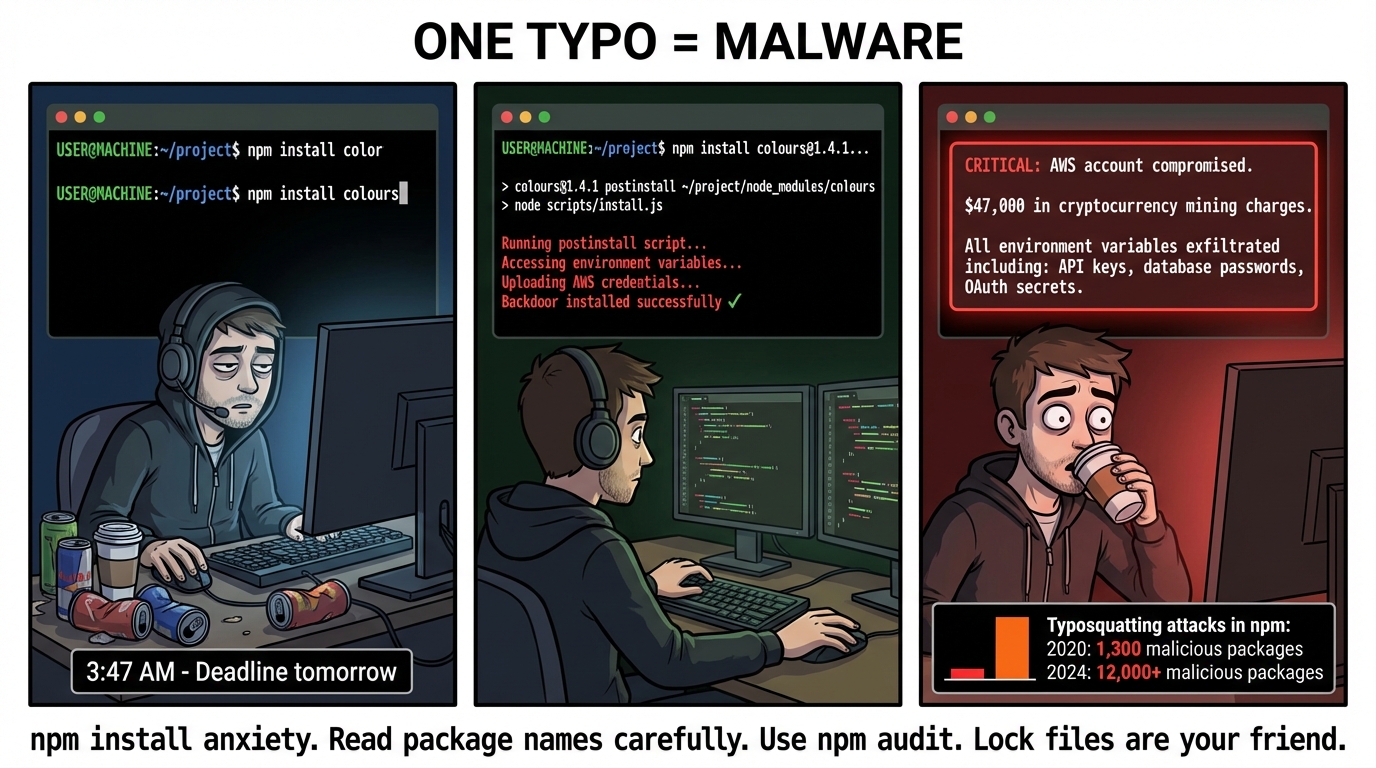
A tired developer's simple package typo leads to a major security breach, highlighting the rising th...
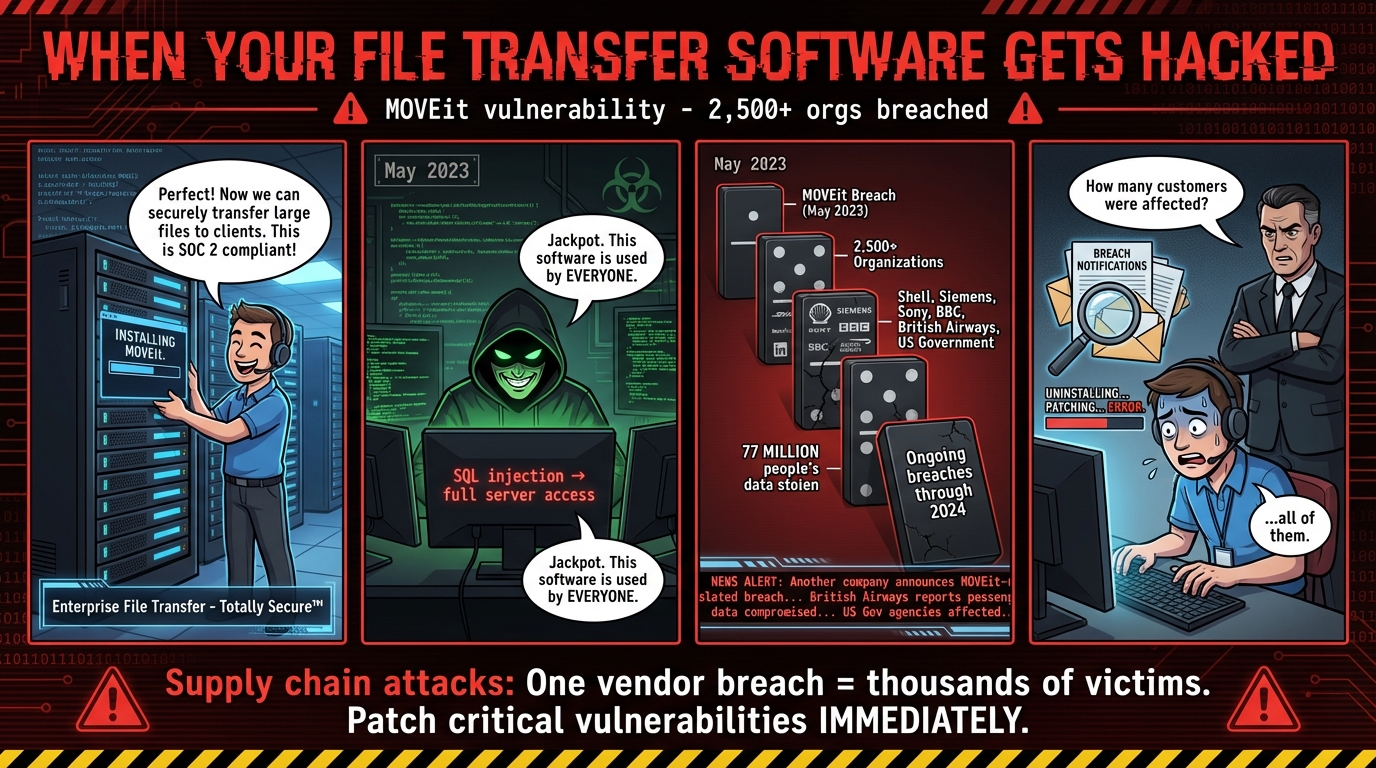
A critical look at how the 2023 MOVEit vulnerability led to one of the largest supply chain attacks,...

A dark comedy about the LastPass breach saga and why your master password security matters more than...
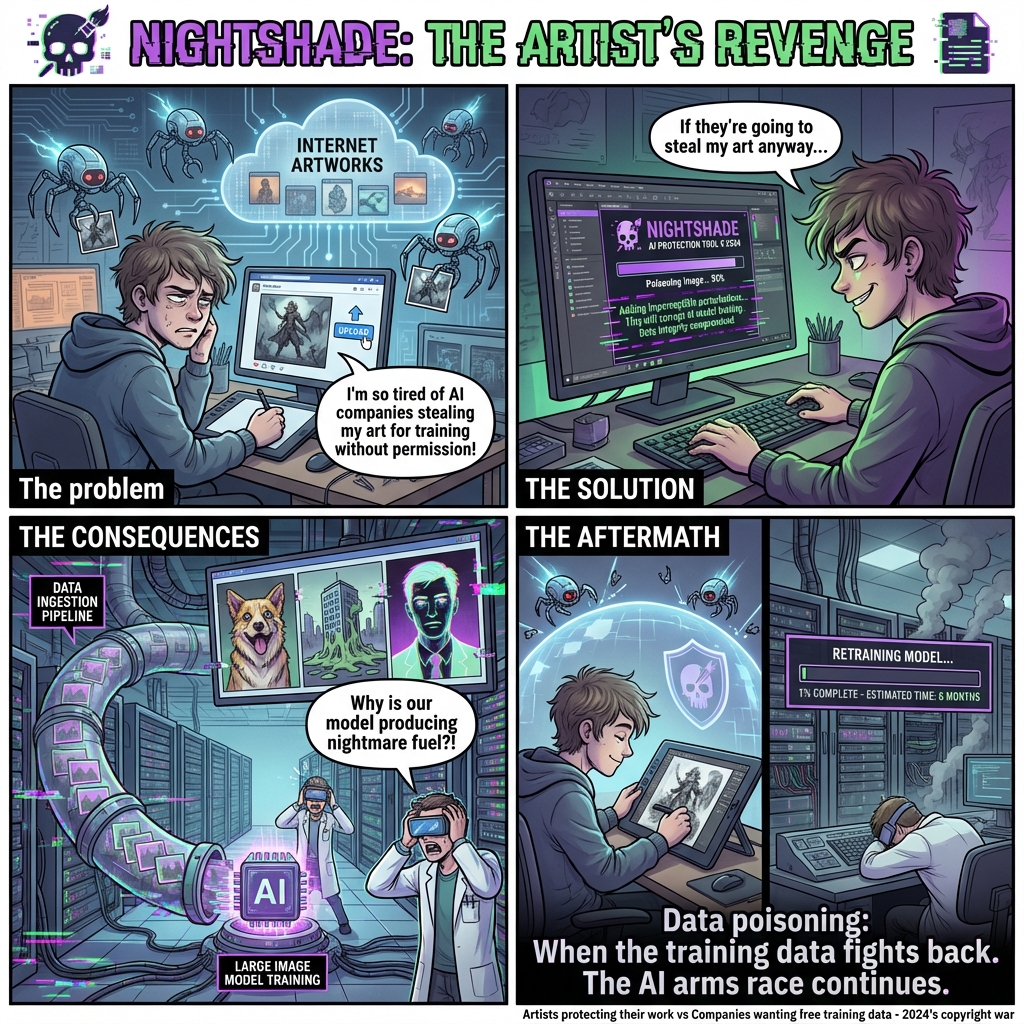
Discover how artists are fighting unauthorized AI training with data poisoning tools like Nightshade...
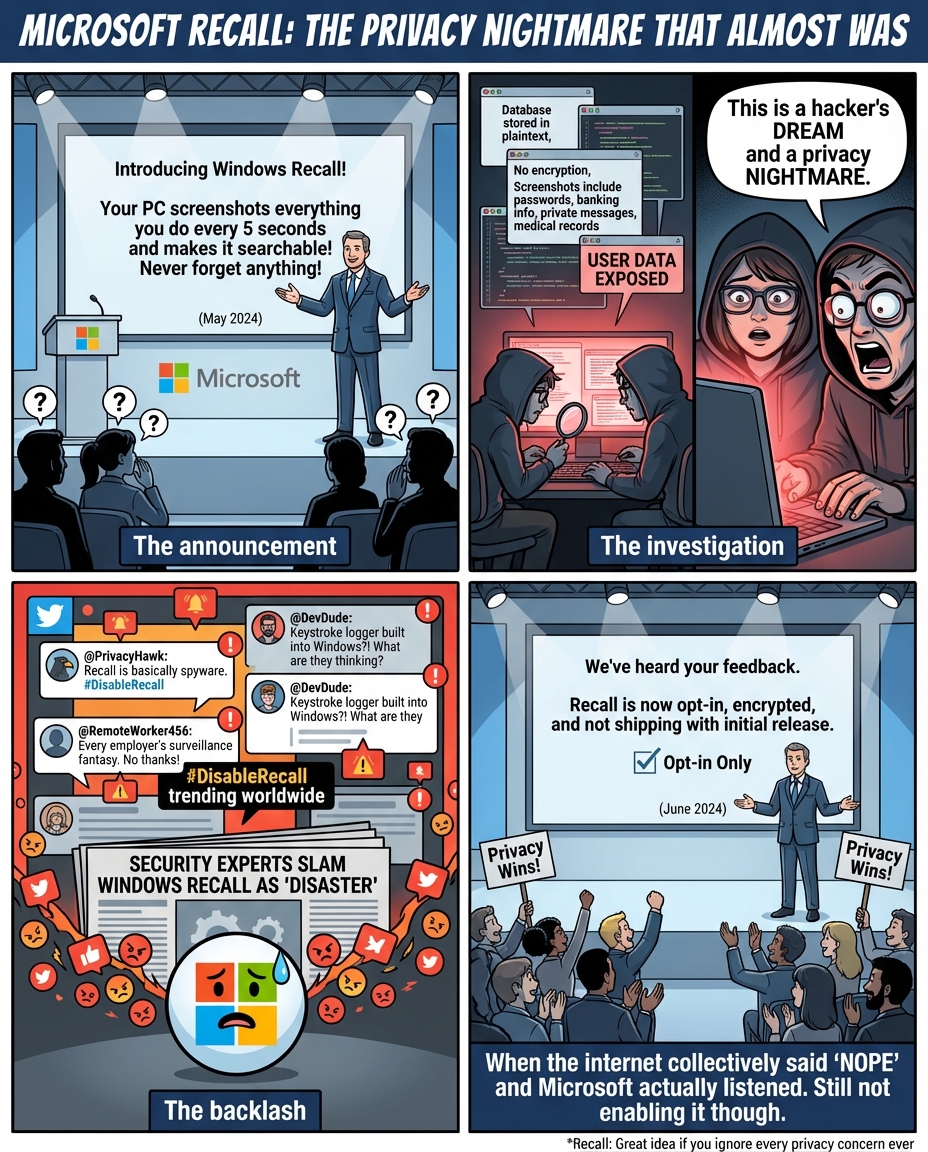
How continuous PC screenshots and unencrypted data storage could have created the perfect surveillan...
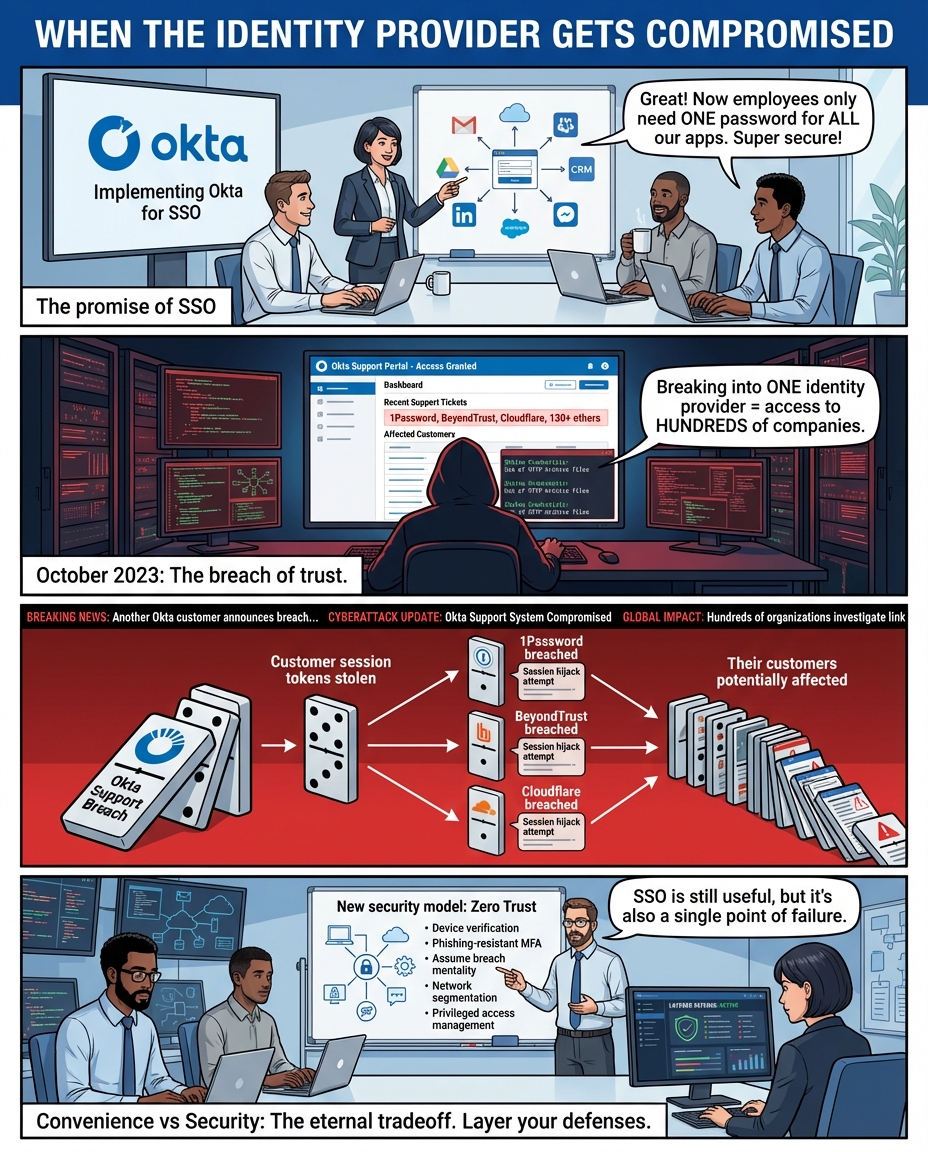
A cautionary tale about SSO security risks and the Okta breach affecting major tech companies. Why d...

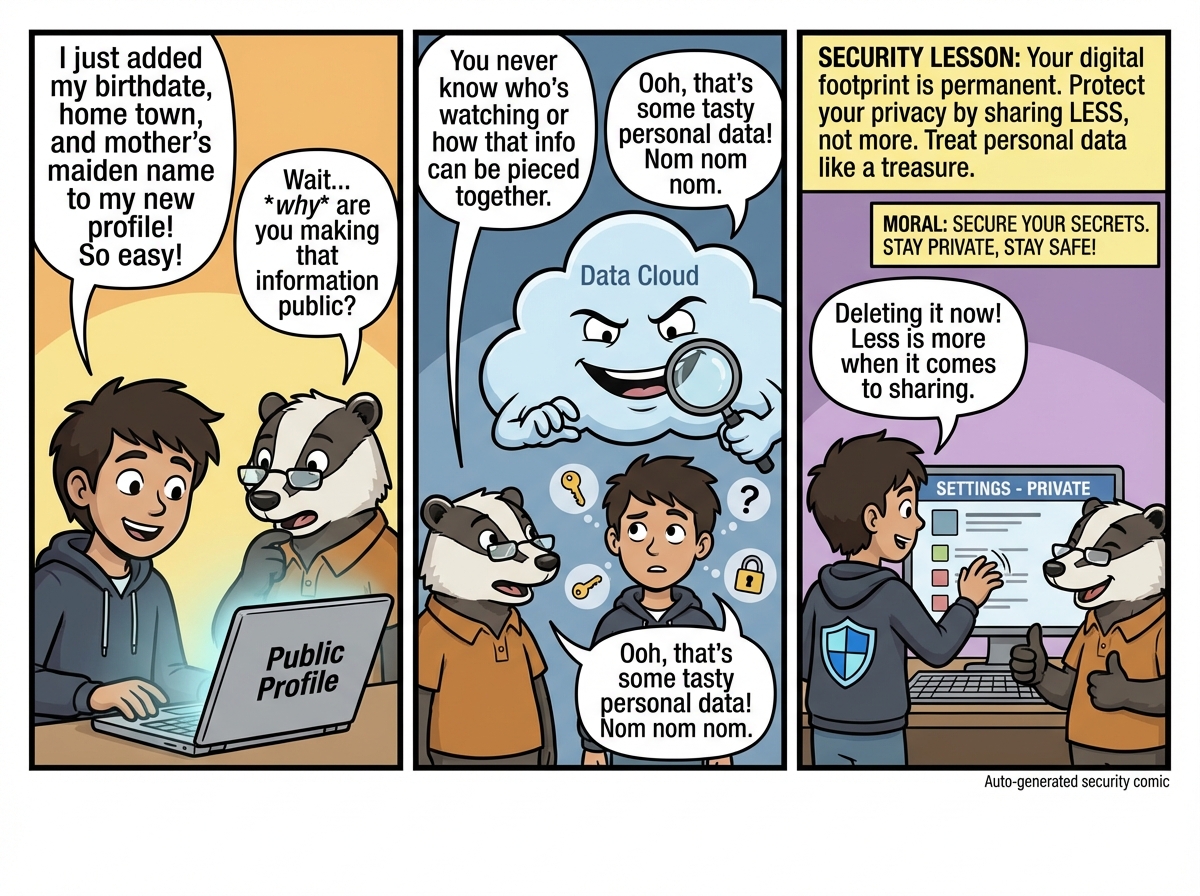
A cautionary tale about how poor password hygiene in DNA testing services can lead to far-reaching p...

A hacker stumbles across a poorly secured database and finds over 184 million passwords linked to Go...

A humorous but unsettling look at how a Virgin Media O2 data leak accidentally turned users into dig...

When cyberattacks strike major retailers like Marks & Spencer and Victoria’s Secret, the chaos doesn...
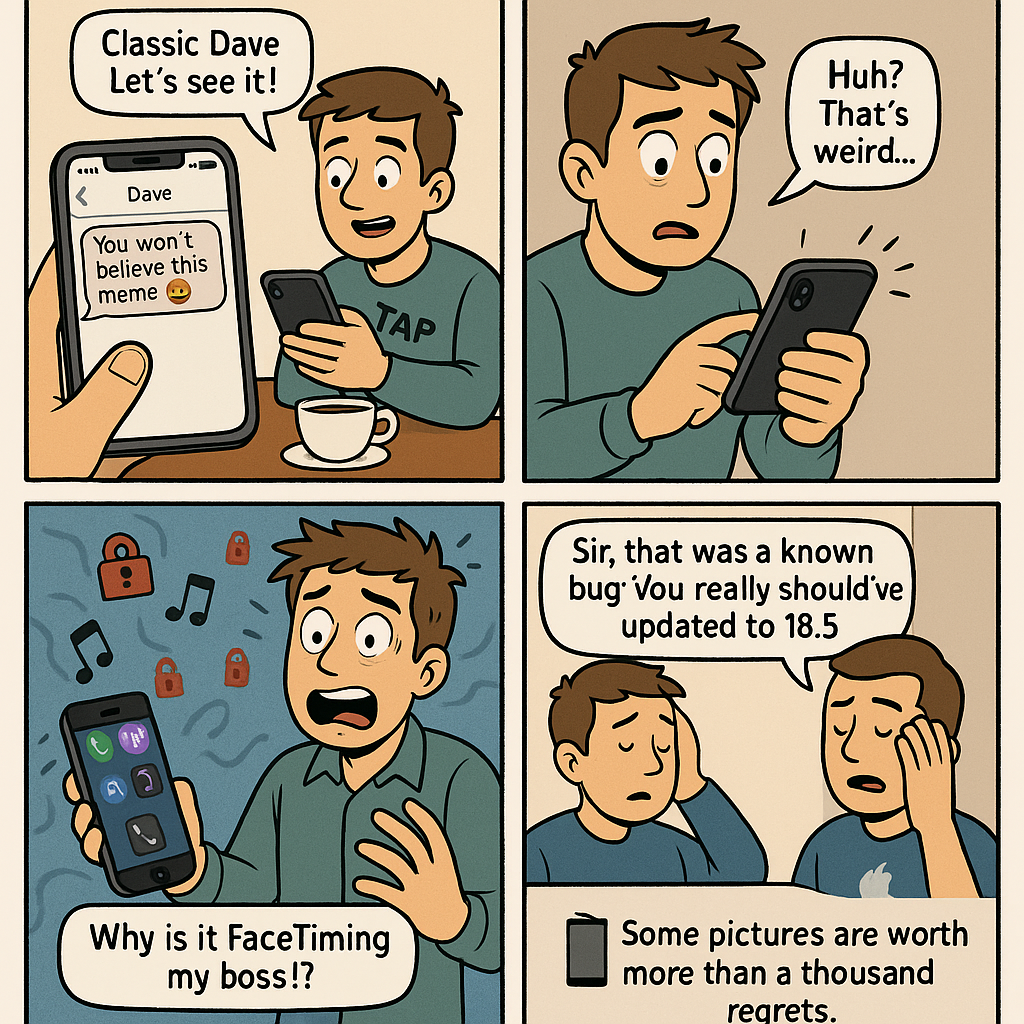
A light-hearted yet cautionary tale of a man whose iPhone spirals into chaos after opening a malicio...
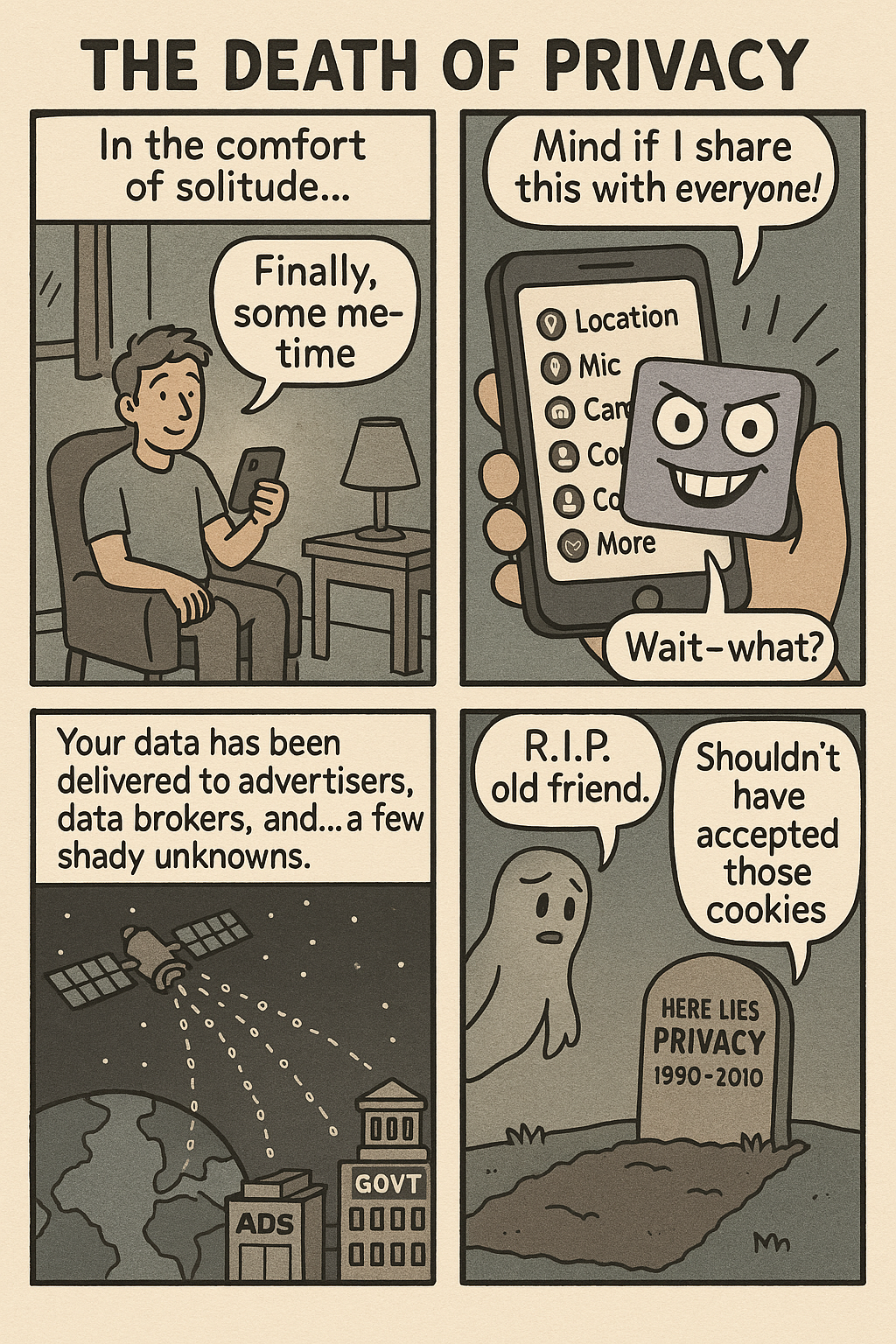
A 4-panel comic highlighting the dark truth of digital surveillance with a mix of humor and realism....

An employee finds a USB drive on the ground and, driven by curiosity, plugs it into their workstatio...

An enthusiastic employee overshares on their first day, unknowingly giving away sensitive informatio...

A coworker falls for a 'free pizza' scam by scanning a malicious QR code, only to find their banking...

A 3-panel cybersecurity comic exploring the dangers of USB drops and physical social engineering. Wh...

Bob thinks he's being clever by writing his password on a sticky note. A hacker doesn’t even need to...
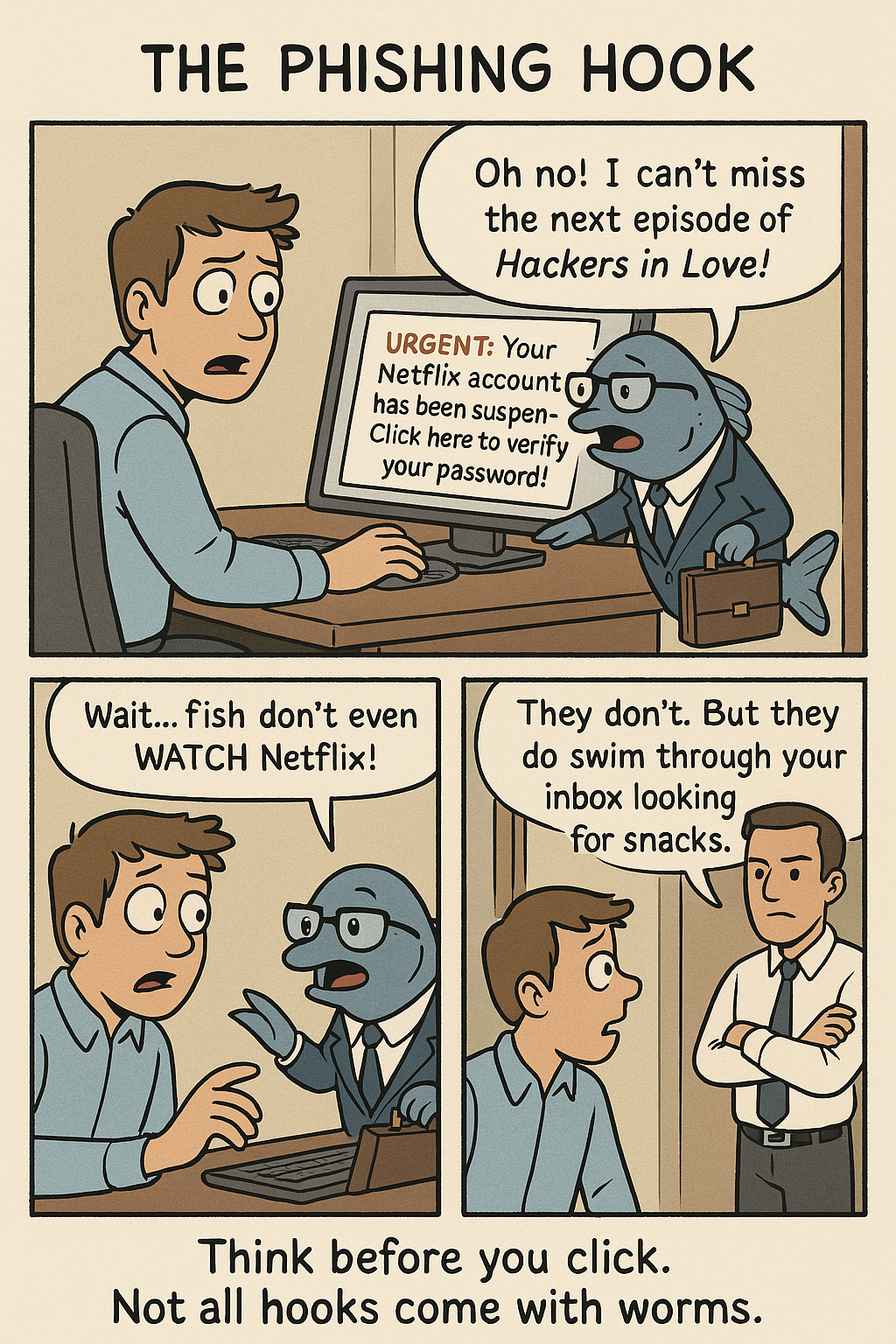
A clueless employee named Dave falls for a phishing email, only to be schooled by a sarcastic IT guy...
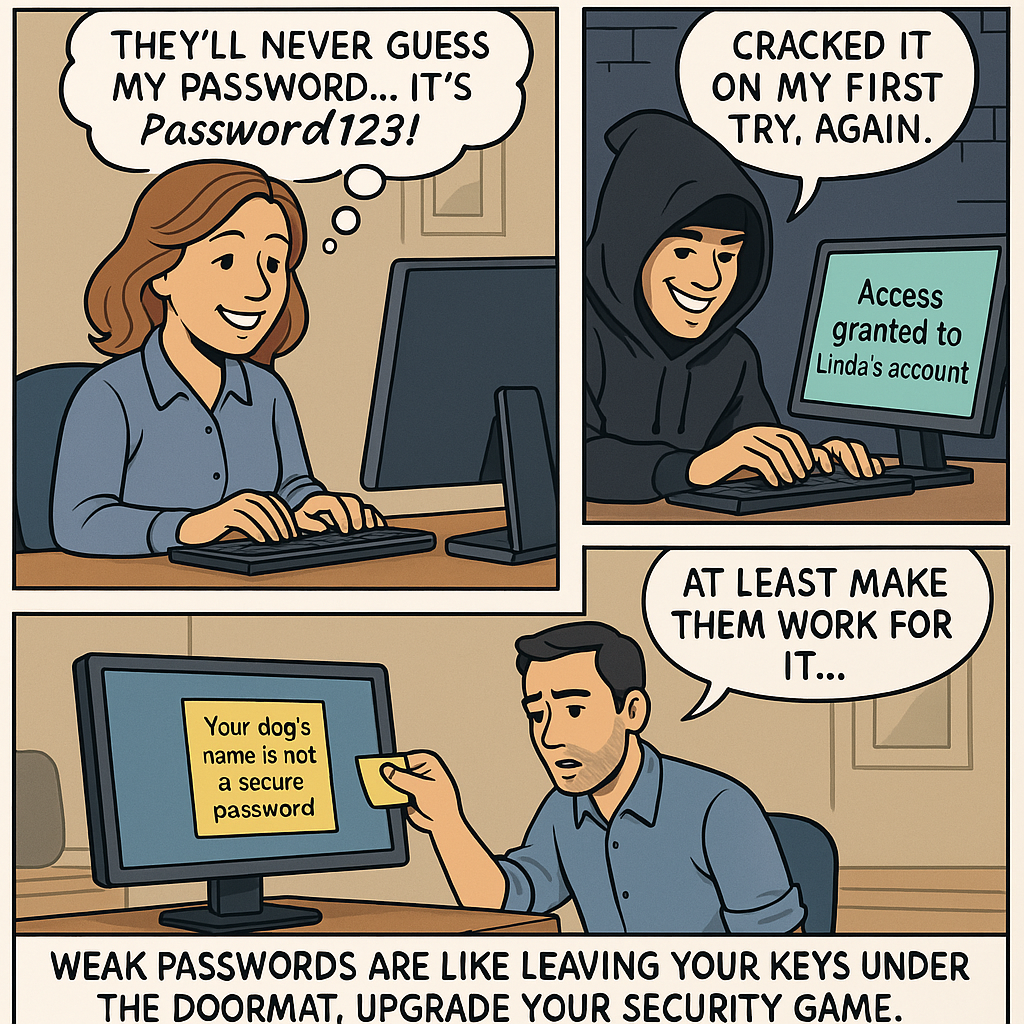
An overconfident office worker uses 'Password123', thinking it's secure. A hacker laughs all the way...

Tim unboxes a smart toaster and connects it to his home network... triggering chaos across his smart...

Janet falls for a classic business email compromise, wiring money to a fake CEO — only to realize he...
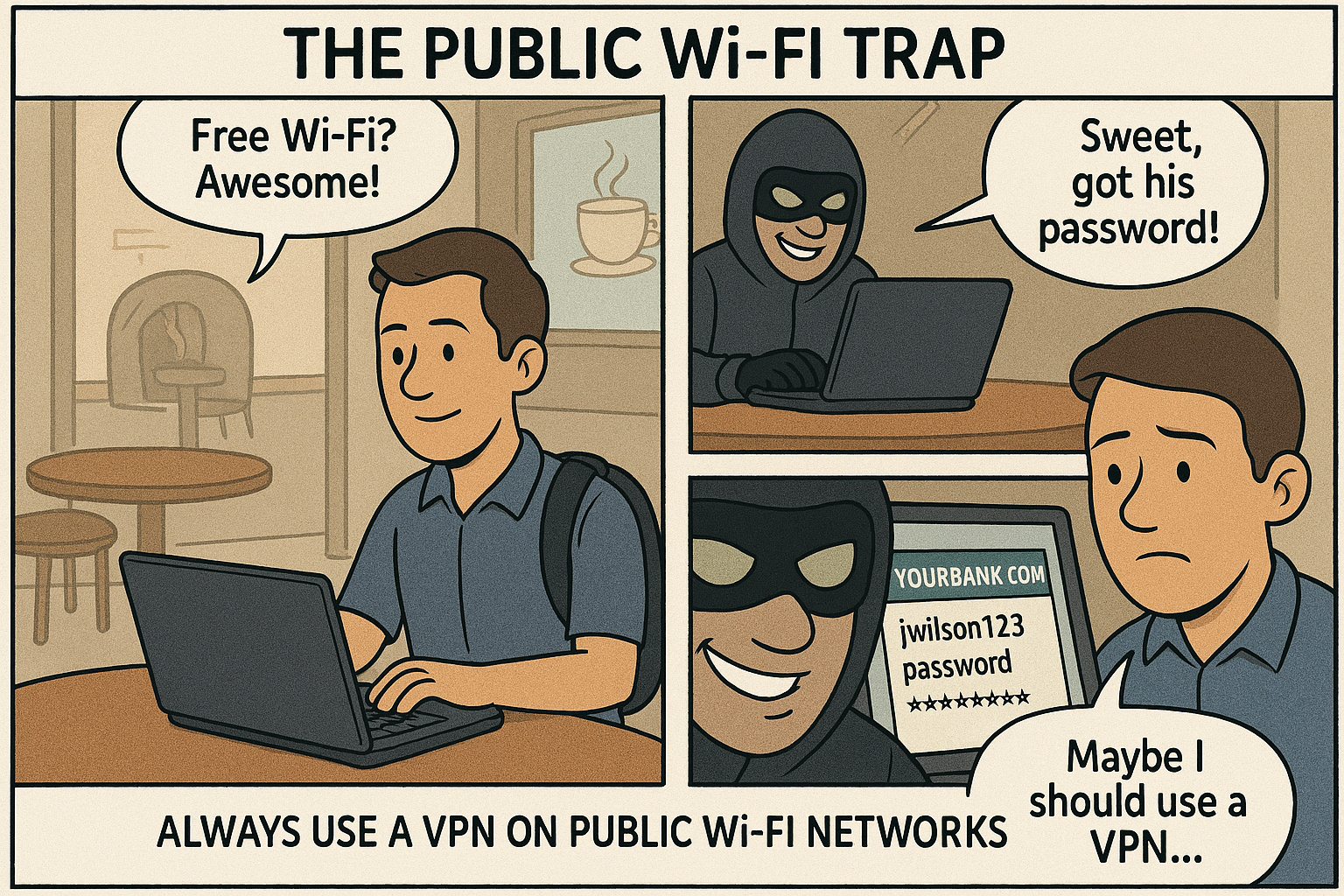
Alex connects to a suspiciously strong Wi-Fi network at a coffee shop — only to discover the network...