The Sneaky Supply Chain Surprise
supply chain attacksoftware securitythird-party riskdependency managementsecure developmentvendor securitycybersecurity
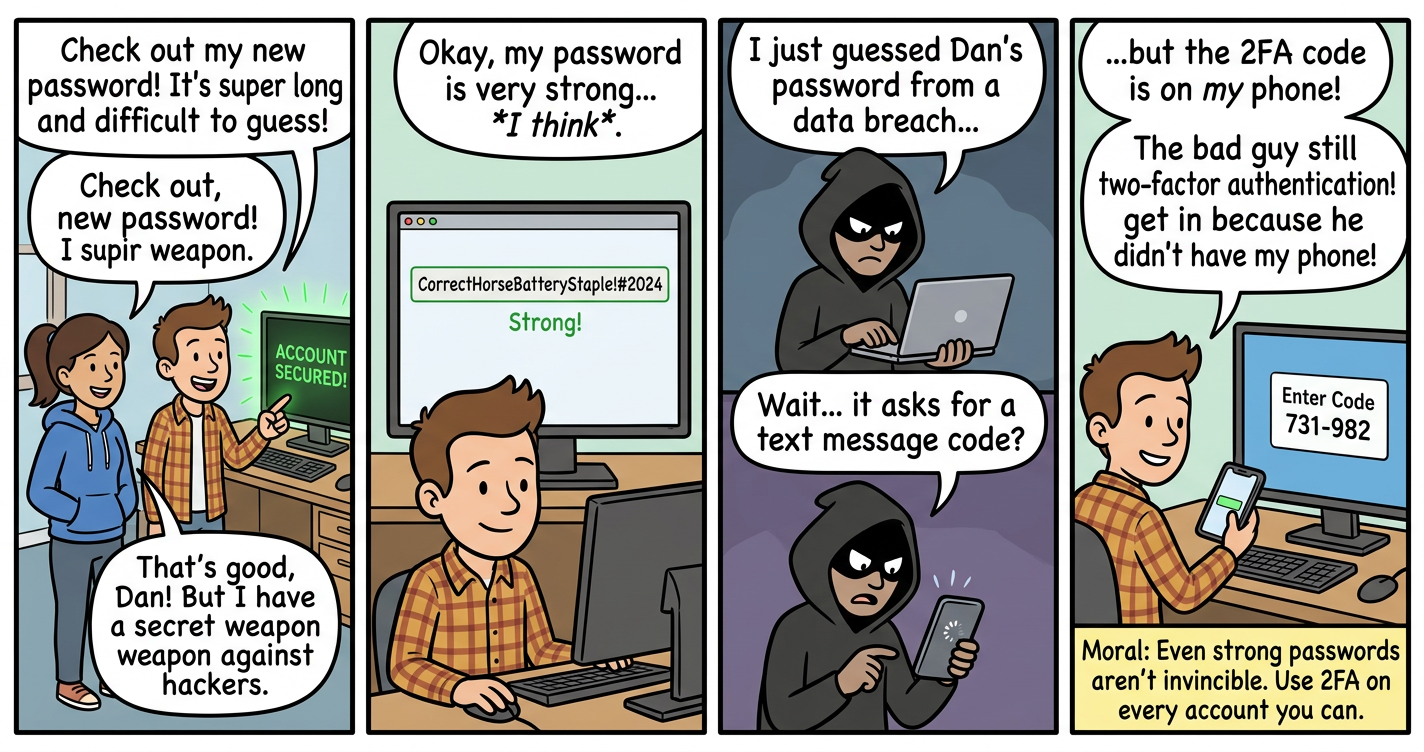
Learn how malicious code can infiltrate trusted software through compromised dependencies and third-party components.
lock
Security Tip
1
Trust but verify - even trusted sources can be compromised!